
SMB Tech & Cyber Newsletter | CPF Coaching
120 episodes — Page 1 of 3

5 Critical Security Alerts from Last Week: Copilot Bugs, Bluetooth Hacks, and New Privacy Laws
January 2026 Alert: Critical Microsoft Copilot vulnerability (Reprompt), Bluetooth "WhisperPair" exploit affecting Sony/Google devices, and new privacy laws in IN, KY, & RI. Get the executive summary and 30-day mitigation plan for SMBs. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

AI, Identity, and Breaking Into Cyber: CEO Jasson Casey’s Blueprint for Success
From building software to defending it: Jason Casey (CEO, Beyond Identity) shares his journey from Software Engineer to Cybersecurity Expert. Discover why mastering network protocols and engineering fundamentals is the secret to a successful cyber career. Listen now on Breaking into Cybersecurity. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

The Glass House: Why 2026 is the Year We Must Audit Our "Agents" and "Avatars"
CES 2026 changed the threat landscape. From "Superuser" AI agents to "cute" surveillance robots like Mirumi, we outline the top 4 trends SMB tech leaders must address immediately to secure their organizations. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

3 Urgent Cyber Threats Costing SMBs Millions (2025 Update)
Urgent briefing for US SMBs: Critical patches needed for WatchGuard, Fortinet, & Cisco. Discover how to stop AI attacks and avoid $3M breach costs. Read the Urgent briefing for US SMBs: Critical patches needed for WatchGuard, Fortinet, & Cisco. Discover how to stop AI attacks and avoid $3M breach costs. Read the plan. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Don't Boil the Ocean: A Cost-Effective Architecture for CMMC Level 2
CMMC Phase 1 is effective as of Nov 2025. DIB leaders: Get the strategic guide to CUI, VDI, and NIST 800-171 compliance before the 2026 deadline. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

The Silent Kill Switch: Why Your Business Needs a "Human" Disaster Recovery Plan
Is your business one tragedy away from collapse? Learn how to mitigate "Key Person Risk" and the "Bus Factor" with our 2025 guide to IT succession planning. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Your CEO and Your Sales Team Don't Face the Same Threats.
The “One-Size-Fits-All” ProblemWe’ve all been there. A mandatory, hour-long cybersecurity training video that covers everything from phishing to physical security in a bland, generic way. Your marketing team is half-listening while thinking about their next campaign, and your finance department is wondering how any of this applies to their daily invoice processing. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Breaking into Cybersecurity: An In-Depth Conversation with Eric Stride
In the latest episode of “Breaking into Cybersecurity,” host Chris Foulon sits down with Eric Stride, the Chief Security Officer at Huntress. Eric’s journey into cybersecurity is not only inspiring but also enlightening for anyone looking to enter this ever-evolving field. With over two decades of experience in the military and private sectors, Eric shares his insights on career development, leadership, and the future of cybersecurity. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Quantum Computing: Your Next Great Opportunity
Quantum Computing: The Future of Innovation and Security In this episode, we explore the revolutionary impact of quantum computing on the future of technology, innovation, and security. Learn about the key differences between classical bits and quantum qubits, and how superposition and entanglement enable unprecedented computational capabilities. Discover the strategic opportunities quantum computing presents for industries such as pharmaceuticals, logistics, and artificial intelligence, as well as the urgent cybersecurity threats it poses. Finally, gain actionable insights on how to prepare your organization for the quantum age by conducting risk assessments, exploring post-quantum cryptography, and ensuring crypto-agility. Don't be left behind—embrace this transformative technology and secure your place in the future. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
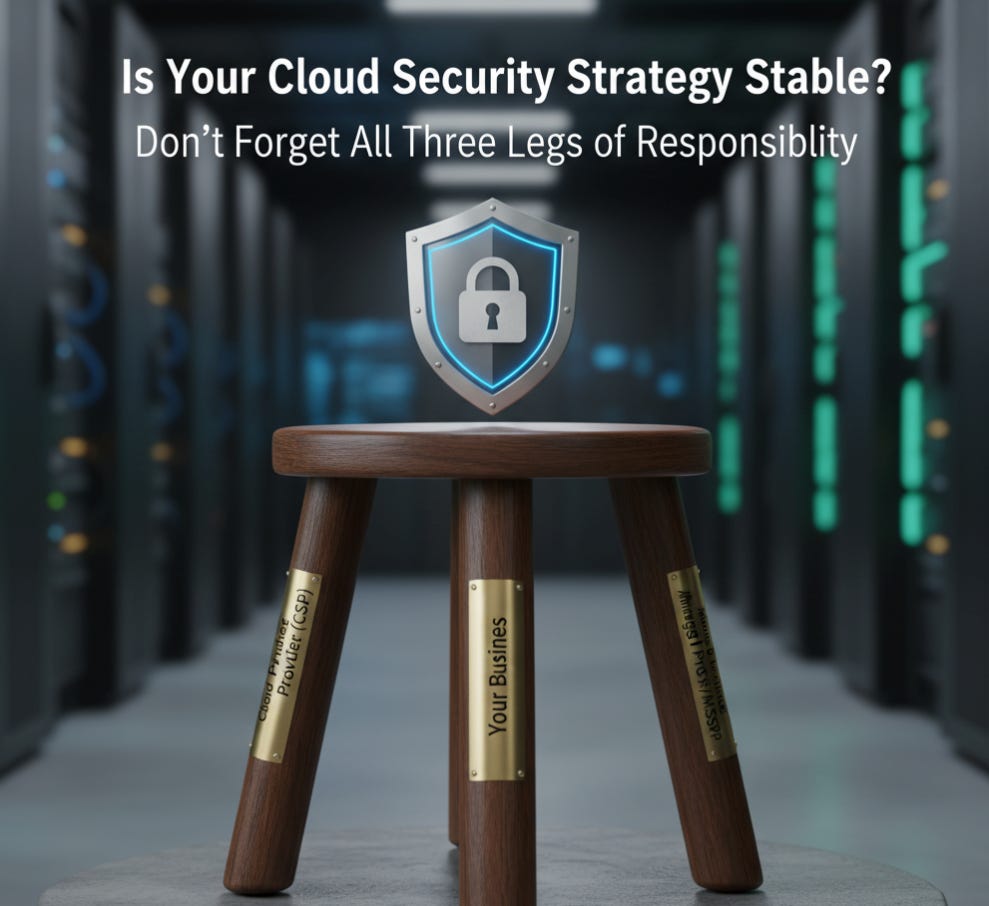
Beyond the Cloud: Mastering the Shared Responsibility Model for Comprehensive Risk Management
Don't assume your cloud provider has you covered. Master the Shared Responsibility Model, build a comprehensive SRM, and align your strategy with frameworks like NIST and CMMC. Read our guide to achieve total accountability. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Navigating the Future of Cybersecurity: Insights from William (Bill) Welser IV
Discover what lies ahead in cybersecurity with technology expert Bill Welser IV. Gain insights into AI's influence, key skills needed, and ways to prepare for the future. From his experience in the Air Force to AI startups, Bill Welser IV discusses his distinctive cybersecurity career path. Explore topics like systems thinking, new technologies, and advancing your career. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Cybersecurity Entrepreneurship: Real-World Advice from Serial Founder Sinan Eren
By Chris Foulon & Sinan ErenIntroductionIn this episode of "Breaking into Cybersecurity," we sat down with Sinan Eren, a seasoned cybersecurity professional, entrepreneur, and founder. Sinan’s journey from a curious hobbyist in Istanbul to a serial founder in Silicon Valley offers a wealth of insights for anyone interested in cybersecurity, entrepreneurship, or both. Here are the highlights and lessons from our conversation.From Hobbyist to Professional: The Early DaysSinan’s entry into cybersecurity wasn’t a deliberate career choice. In the late 1990s, cybersecurity wasn’t even a defined field—just a function of IT. Resources were scarce, and much of the learning happened in underground communities like IRC and through publications like FRAC magazine. For Sinan, curiosity and a desire to experiment led him to discover vulnerabilities and share his findings on platforms like Bug Track, which eventually opened doors to job opportunities.Key Takeaway: Sometimes, passion and curiosity can be more important than formal education in breaking into a new field.Signature-Based vs. Heuristic Security: A Technical EvolutionSinan explained the shift from signature-based antivirus solutions to heuristic and behavioral approaches. Early security tools relied on known patterns to detect threats, but as malware evolved—like the infamous Code Red worm—this reactive approach proved insufficient. The industry began to focus on detecting abnormal behaviors, setting the stage for modern endpoint security.Key Takeaway: The cybersecurity landscape is always evolving. Staying ahead means understanding both the history and the latest trends in threat detection.Entrepreneurship in Cybersecurity: Two PlaybooksSinan’s entrepreneurial journey followed two main playbooks:* The Hype Playbook: Attach security to the latest technology trend (e.g., AI + Security).* The Next-Gen Playbook: Take an existing solution and make it better, faster, or more secure (e.g., reinventing VPNs with Zero Trust Network Access).His first company focused on mobile security, capitalizing on the rise of mobile apps and their security flaws. Later ventures addressed remote access and automation, always driven by real-world needs and feedback from users.Key Takeaway: Successful startups often solve existing problems in new ways or improve on what’s already out there. Listen to the market and adapt.Lessons Learned: Growth, Pivots, and ExitsSinan shared candid stories about the challenges of scaling a startup, including the risks of over-reliance on a single partner and the importance of diversifying your customer base. He emphasized the value of learning from mistakes and knowing when to pivot or sell.Key Takeaway: Flexibility and self-awareness are crucial in entrepreneurship. Sometimes, the best move is to exit and apply your lessons to the next venture.Automation and the Future: Beyond CybersecuritySinan’s latest venture emerged from listening to managed service providers who struggled with operating and automating a growing stack of security tools. By leveraging process mining, UI automation, and AI, his team built solutions that automate repetitive tasks—not just in cybersecurity, but also in finance and other fields.Key Takeaway: The skills and solutions developed in cybersecurity can often be applied to other industries. Don’t limit your vision to a single domain.Advice for Aspiring Professionals and Leaders* For Beginners: The field is more exciting than ever, especially with the rise of AI and LLMs (Large Language Models). Red teaming and offensive security remain fertile ground for creative minds, regardless of background.* For Experienced Pros: Embrace the challenge of integrating AI responsibly. Focus on building guardrails and understanding business processes, not just deploying tools.* For Entrepreneurs: Understand your customers’ workflows and pain points. Document processes, model workflows, and always be ready to adapt your product or business model.ConclusionSinan Eren’s story is a testament to the power of curiosity, adaptability, and listening—both to technology and to people. Whether you’re just starting out or leading a team, the lessons from his journey can help guide your own path in cybersecurity and beyond.To hear the full conversation, listen to the episode of Breaking Into Cybersecurity (and uploaded as the video in this post ;-) The YouTube channel has years of previous conversations)Some security tools you can consider for improving your business security posture:CrowdStrike Falcon: An AI-driven platform for securing your infrastructure at scale and keeping up with AI advancements. https://crowdstrike2001.partnerlinks.io/Cpf-coachingINE Security Awareness and Training is essential for your team to stay updated with the evolving threat landscape, enhancing the effectiveness of the teams supporting your organization. https://get.ine.com/cpf-coachingTenable helps identify weaknesses in your infrastructure, whether on-premises, in the cl
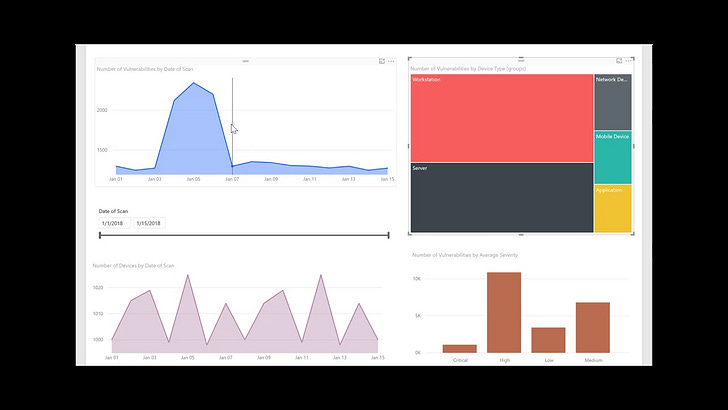
How to Build a Security Culture with Data-Driven Reporting
Foster a true security-first culture by mastering effective cloud security reporting. Learn to translate technical risk into business impact for leadership and technical teams using tools like Microsoft Power BI. Move security from a cost center to a strategic business enabler. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Vulnerability Management Metrics: 15 KPIs to Measure & Mature Your Program
Supercharge your vulnerability management with a data-driven approach! Discover the 15 essential key performance indicators (KPIs) that will help you track your progress, highlight the value of your efforts, and elevate your security program. Embrace actionable metrics to continuously measure, monitor, and enhance your strategy—it's a journey towards a more secure future! This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

The Ghost in Your Cloud: How Hackers Use Social Engineering to Infiltrate and Attack
The Ghost in Your Cloud: How Hackers Use Social Engineering to Infiltrate and AttackUnmasking the "low and slow" identity attacks where threat actors lie in wait within your cloud accounts, and how to fight back before they strike.Discover the new wave of silent cyber threats. Learn how hackers use social engineering to compromise cloud accounts, stay dormant to evade detection, and launch devastating attacks later. Protect your organization now. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Data-Centric Security: Protect Your Cloud Data with Microsoft Defender
Stop chasing every vulnerability. Learn how a Data-Centric Security approach using Microsoft Defender for Cloud helps you discover, classify, and protect your most sensitive cloud data. Prioritize real business risks and prevent impactful breaches. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
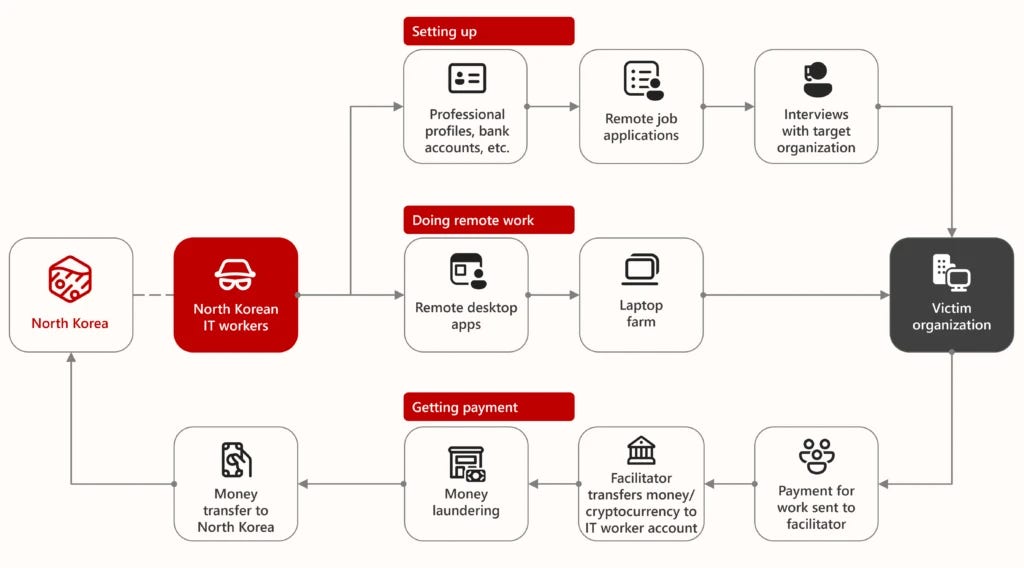
The Phantom Workforce: A Guide to Combating State-Sponsored IT Infiltration
🚀 Transform Your Cybersecurity Approach! 🚀 Join me on a journey through "The Phantom Workforce," where I delve into combating state-sponsored IT infiltration. Equip yourself with knowledge and strategies to protect your organization's sensitive information from modern threats. Let's enhance our cyber defenses together! #cyberawareness #protectyourdata #ITinfiltration This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Develop and Enforce Robust Remediation Policies and SLAs
Strengthen your organization's security response with robust Remediation Policies and SLAs! Discover how to transform your vulnerability management program into a mature, auditable business function that ensures accountability and timely risk reduction. Learn more about the essential components of a successful policy in our latest discussion. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

From Psychology to Cybersecurity: Craig Taylor's Impact
In this episode of Breaking into Cybersecurity, host Chris welcomes Craig Taylor, CEO of Cyber Hoot, as he shares his inspiring journey into the cybersecurity industry. Known for his role as a virtual CISO and cybersecurity awareness advisor, Craig discusses how he began his career with a psychology degree and eventually transitioned into cybersecurity. He delves into the importance of positive reinforcement over punishment in cybersecurity training and the evolving role of AI in detecting and mitigating threats. Craig also offers valuable advice for those looking to enter the field and emphasizes the need for organizations to understand and manage AI-related risks. Tune in for insights on cybersecurity, AI advancements, and practical tips to enhance cybersecurity awareness. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Embed Security into the DevOps Lifecycle (DevSecOps)
Learn to "shift left" with DevSecOps. Discover how to integrate security into your development lifecycle, from Infrastructure as Code (IaC) scanning to container analysis, using Microsoft Defender for Cloud to build a proactive, code-to-cloud security posture. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Navigating the Cybersecurity Career Path: Insights from CISO Tradecraft with Guest Christophe Foulon
In a recent episode of CISO Tradecraft, host G Mark Hardy sat down with cybersecurity expert Christophe Foulon to explore the intricacies of entering and thriving in the cybersecurity industry. Christophe, a seasoned professional and podcast host, shared his wealth of experience and offered valuable insights for anyone considering a career in cybersecurity or looking to advance within the field. Breaking into Cybersecurity The episode began with a discussion about the challenges and rewards of breaking into cybersecurity. Christophe highlighted his own journey, starting from a help desk role and eventually transitioning into cybersecurity. He emphasized the importance of staying current with certifications and the ever-evolving nature of the industry. "Technology moves along with or without us," Christophe noted, emphasizing the necessity of continuous learning. Understanding the CISO RoleA key focus of the conversation was the allure of the CISO (Chief Information Security Officer) title and its associated responsibilities. Christophe pointed out that while the title and paycheck might seem attractive, the reality involves continuous learning, long hours, and high-pressure situations. He stressed the importance of understanding these demands before aspiring to such a position. The Importance of Leadership and OwnershipChristophe shared that becoming a successful CISO requires more than just technical expertise. It involves political and management skills, and the ability to communicate effectively with the board and other executives. He also emphasized the need for CISO candidates to have political awareness and the capacity to work with stakeholders to own and manage risk. Building a Strong Cybersecurity Team Leadership was another crucial topic discussed. Christophe underscored the importance of understanding personal motivations and career aspirations within a team. By aligning roles with individual strengths and desires, leaders can foster productivity and satisfaction. He advocated for methods like personality assessments and one-on-one conversations to optimize team dynamics. Leveraging NeurodiversityA particularly insightful part of the discussion revolved around the role of neurodiversity in cybersecurity. G Mark Hardy and Christophe agreed that cybersecurity often attracts neurodiverse individuals, whose unique skills can become superpowers within the field. Ensuring these individuals find roles that align with their strengths not only enhances organizational productivity but also boosts individual fulfillment. Advice for Aspiring CISOs and New EntrantsChristophe provided guidance for those considering a career as a fractional or virtual CISO, emphasizing the importance of understanding legal responsibilities and setting clear scope and expectations with clients. He also advised on staying true to one’s passions to prevent burnout. Conclusion and Contact Information The episode wrapped up with Christophe encouraging strategic thinking in both career development and cybersecurity program planning. For those interested in learning more from Christophe, his resources, including his podcast "Breaking into Cybersecurity" and books, are available on platforms like YouTube, Apple Podcasts, and Amazon. Additional information can be found on his website at christophefoulon.com. CISO Tradecraft continues to provide invaluable content for cybersecurity professionals seeking to elevate their careers and leadership skills. As the industry evolves, the lessons from thought leaders like Christophe Foulon remain crucial for both personal and professional development. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

CISO Trade Craft Podcast with Guest Christophe Foulon
In this episode of CISO Tradecraft, host G Mar welcomes Christophe Foulon, founder of CPF Coaching LLC. Christophe shares insights on enabling businesses to use technology safely through strategic planning, risk management, and tailored cybersecurity measures. He emphasizes the importance of a holistic approach to security, addressing people, processes, and technology to enhance business resilience. Christophe also discusses his efforts in developing leaders within organizations and his support for the community through his podcast and involvement with various non-profits. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Automate Remediation and Response with Security Orchestration
Ditch slow manual processes. Discover how security automation and SOAR reduce human error, accelerate threat containment, and free up your security analysts. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Cloud Security: Identity as the New Perimeter | JIT & Adaptive Access
Discover how a robust Identity and Access Management (IAM) strategy, with JIT access and adaptive controls, can transform your cloud security and virtually patch vulnerabilities. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Overwhelmed by Alerts? A Guide to Risk-Based Prioritization Over CVS
Discover how to mature your vulnerability management from a reactive chore to a continuous, risk-based program. This guide helps leaders protect their multi-cloud enterprise, prevent data breaches, and measurably reduce business risk. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Navigating Third-Party Risk Management: Essential Strategies for SMBs
Mastering Third-Party Risk Management for SMBsIn today's interconnected business environment, SMBs increasingly rely on third-party vendors and partners, heightening risk factors. This episode dives into essential strategies for effective Third-Party Risk Management (TPRM). Learn to inventory and assess third-party relationships, conduct thorough due diligence, set clear contractual requirements, and continuously monitor and reassess security postures. Discover how to form incident response plans, train your team effectively, and leverage external resources to bolster your TPRM program. Enhance your cybersecurity approach to safeguard assets, reputation, and customer trust. For personalized assistance, contact [email protected]. Plus, discover how easyDMARC can ensure your emails reach their intended destination. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
10 Best Practices for the Modern Enterprise: Achieve Complete Attack Surface Visibility
Discover how to mature your vulnerability management from a reactive chore to a continuous, risk-based program. This guide helps leaders protect their multi-cloud enterprise, prevent data breaches, and measurably reduce business risk. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Strengthening Your Digital Defense: Practical Cybersecurity Approaches for SMB Tech Executives in 2025
The cyber environment presents ongoing challenges with increasing cyber threats, and Small to Medium Businesses (SMBs) often find themselves particularly at risk. Although high-profile breaches frequently make the news, SMBs are sometimes targeted because they are viewed as more vulnerable and have limited resources, making them what some might call "low-hanging fruit" for cybercriminals. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Review of the 2025 Verizon DBIR
The 2025 Verizon DBIR is out! Learn the critical cybersecurity shifts impacting SMBs: soaring third-party risks, rising espionage, persistent ransomware, and the continued threat of credential abuse. Get actionable insights for stronger defenses. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Navigating CMMC 2.0: A Strategic Imperative for Tech Leaders Protecting CUI
Navigate CMMC 2.0 compliance for government contractors protecting CUI. Understand the 3 levels, key requirements, and how it compares to FedRAMP and DoD Impact Levels. Learn about Microsoft GCC High for CMMC readiness. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Crafting an Effective Overall Risk Management Plan for SMBs from Scratch
Small and medium-sized enterprises (SMBs) increasingly rely on digital presence, facing IT and business challenges. Tech leaders launching initiatives need a robust risk management strategy that is careful yet efficient. This report provides SMBs with a comprehensive template that combines industry insights, risk management best practices, and case studies to recognize, evaluate, and mitigate risks while aligning with business goals. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Navigating NIST 800-171 Compliance: A Strategic Guide for SMBs
Discovering NIST 800-171 & CMMC ComplianceThe threat landscape is filled with growing cyber risks, making it vital for organizations to protect sensitive information. This is particularly critical for Small and Medium-sized Businesses (SMBs) operating within the Defense Industrial Base (DIB), where safeguarding Controlled Unclassified Information (CUI) is not just a matter of security but a prerequisite for survival. The National Institute of Standards and Technology (NIST) Special Publication 800-171 is the cornerstone for this protection in non-federal systems. Furthermore, the Cybersecurity Maturity Model Certification (CMMC) 2.0 framework builds upon NIST 800-171, underscoring its importance. For SMBs in the DIB, achieving and maintaining compliance is not merely a regulatory hurdle; it represents a strategic imperative for accessing Department of Defense (DoD) contracts and ensuring the long-term viability of their business.1 NIST SP 800-171 provides the necessary guidelines and requirements for protecting this sensitive government data, making its adherence a contractual obligation for organizations that handle CUI.4The Dual Challenge and Opportunity: Balancing Security with SMB RealitiesWhile the importance of cybersecurity compliance is evident, SMBs often face a unique set of challenges in achieving NIST 800-171 and CMMC compliance. Limited resources, financial constraints, a scarcity of dedicated personnel, and a lack of in-house cybersecurity expertise frequently present significant obstacles.6 Implementing NIST SP 800-171 using only internal resources can demand a substantial investment of time and money, potentially straining the already tight budgets of smaller organizations.13 Furthermore, the technical and often intricate requirements of both NIST 800-171 and CMMC require specialized cybersecurity knowledge that many SMBs may lack internally, making accurate interpretation and practical implementation considerable challenges.7 The daily demands of running a small business often leave owners and employees with stretched schedules, making it difficult to allocate the dedicated time required for thorough compliance planning, implementation, and the creation of necessary documentation.7 Adding to this complexity is the fact that cybersecurity standards are not static; NIST 800-171 and CMMC are subject to revisions and updates, requiring SMBs to commit to ongoing monitoring and adaptation of their security practices to maintain a compliant posture.7 Finally, accurately identifying all instances of Controlled Unclassified Information (CUI) within an SMB's diverse IT environment and implementing the appropriate technologies for its effective management and protection can be a particularly challenging aspect of compliance.7Despite these considerable challenges, achieving NIST 800-171 compliance presents significant opportunities for SMBs within the defense sector. Compliance is a key that unlocks access to the substantial and often high-value contracting opportunities available within the Department of Defense and its extensive network of partners.1 By implementing the security controls and measures mandated by NIST 800-171, SMBs significantly strengthen their defenses against various cyber threats, including data breaches, malware attacks, and unauthorized access, leading to a more resilient and secure business operation.1 Adhering to recognized cybersecurity standards such as NIST 800-171 sends a powerful message to customers, clients, and partners, showcasing a strong commitment to data security and privacy, which fosters greater trust and strengthens business relationships.1 Achieving NIST 800-171 compliance can also set an SMB apart from its competitors, particularly when vying for government contracts or seeking partnerships with larger organizations that prioritize robust cybersecurity practices, providing a distinct edge in the marketplace.1 Furthermore, by complying with NIST 800-171, SMBs can significantly reduce the likelihood and impact of data breaches, thereby mitigating potential reputational damage, avoiding costly legal repercussions, and safeguarding their business continuity.1 NIST 800-171 also includes specific requirements for developing and documenting an incident response plan, equipping SMBs with the necessary strategies and procedures to react swiftly and effectively to security incidents, minimizing potential damage and downtime, and enhancing overall business resilience.15 Finally, although there is an initial investment, the proactive measures taken to prevent cyber incidents through NIST 800-171 compliance can result in substantial long-term cost savings by avoiding the significant financial burdens often associated with data breach recovery, legal actions, and reputational damage repair.15Decoding the Frameworks: Understanding NIST 800-171 and CMMC 2.0NIST Special Publication 800-171 is a set of security guidelines and requirements designed to protect Controlled Unclass
Combating Security Platform Fatigue: A Strategic Approach to Tool Consolidation
Discover how to combat security platform fatigue by strategically consolidating tools around your primary security provider while filling gaps with specialized solutions. Learn practical approaches to reduce complexity, improve visibility, and enhance your security posture without overwhelming your team. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Safely Implementing AI for SMBs
Discover how SMBs can boost productivity by safely using AI in areas like customer service, marketing, inventory, and cybersecurity. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
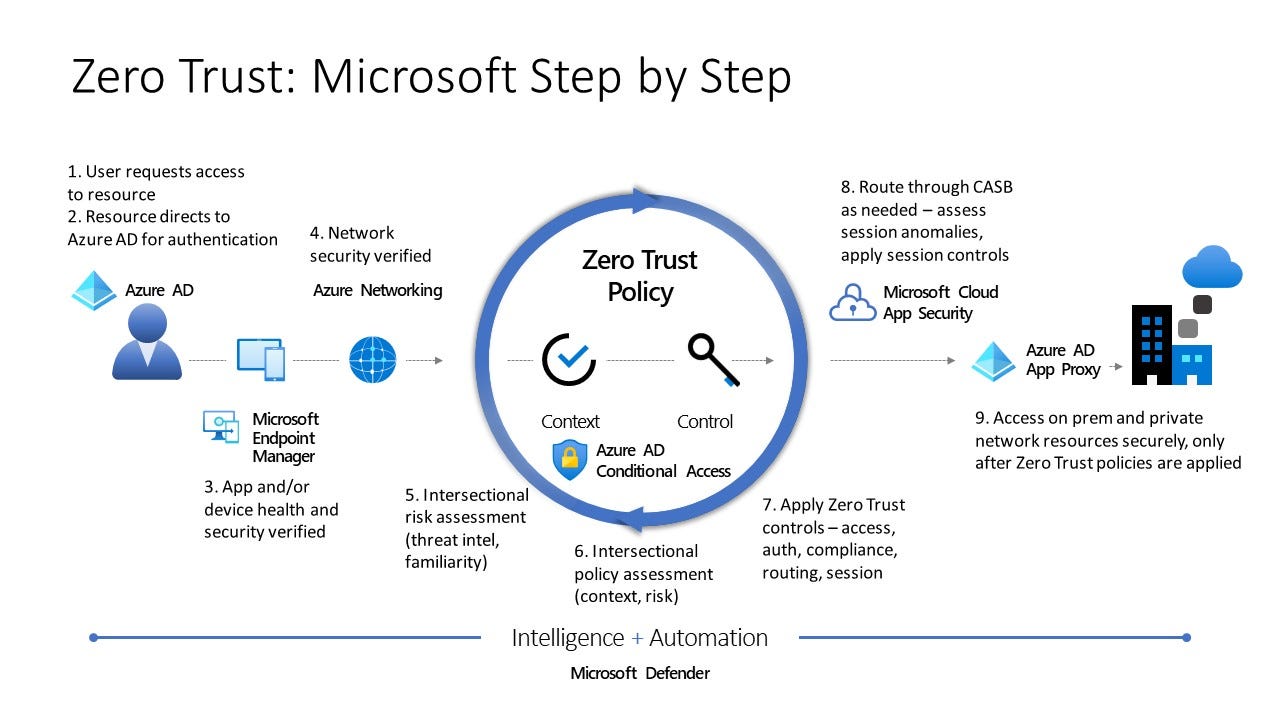
Implementing Zero Trust Security for Small and Medium Businesses with Microsoft Solutions
Learn how small and medium businesses can enhance their cybersecurity with a Zero Trust strategy using Microsoft solutions. Discover practical steps to protect your business from evolving threats This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Proposed 2025 HIPAA Security Rule Changes & SMB Implications
The 2024 HIPAA Security Rule amendments represent a significant overhaul, demanding strategic realignment of governance, risk management, and compliance (GRC) programs, particularly for SMBs. The proposed rule changes have an open commentary period, which ends on March 7th, 2025. To leave comments, go here: https://www.federalregister.gov/documents/2025/01/06/2024-30983/hipaa-security-rule-to-strengthen-the-cybersecurity-of-electronic-protected-health-information SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.The elimination of the "addressable" implementation specifications, expanded technical safeguards, and compressed implementation timelines create compliance obligations and opportunities for strengthening organizational resilience. To navigate these changes successfully, SMBs must prioritize a phased approach, leveraging cost-optimization strategies and cultural change initiatives. The key is to transform compliance from a burden into a strategic advantage. Failing to adapt puts SMBs at considerable risk, as demonstrated by the statistic that "60% [of SMBs] fail within six months of a breach."1. Core Changes to the HIPAA Security Framework:* Elimination of "Addressable" Implementation Specifications: The removal of the distinction between "required" and "addressable" safeguards is a fundamental shift. The revised rule "mandates implementation of all security controls unless specific documented exceptions apply." This directly addresses the previous tendency of SMBs to treat these standards as optional. Specific examples now mandated include:* Multi-Factor Authentication (MFA): "Now required for all system access points handling ePHI, replacing previous conditional implementations."* Encryption: "Mandatory for ePHI both at rest and in transit, closing previous loopholes for internal network communications."* Network Segmentation: "Requires documented segmentation strategies preventing lateral movement during breaches."* Expanded Technical Safeguards: The updated Technical Safeguards (45 CFR §164.312) introduce 14 new implementation specifications aligning with NIST Cybersecurity Framework standards. This expansion creates "technical debt requiring immediate prioritization" for SMBs. Examples of the added or emphasized safeguards include:* Maintaining comprehensive technology inventories updated quarterly.* Developing network topology maps tracking ePHI flow across systems.* Implementing session timeout policies for inactive systems.* Extending workstation security controls to mobile devices.* Automated patch management within 30 days of release.* Removal of unnecessary software from ePHI systems.2. GRC Program Transformations:* Integrated Risk Management Frameworks: The updates mandate alignment between HIPAA compliance and enterprise risk management programs. Key integration points include:* Unified risk register (mapping HIPAA vulnerabilities to corporate risk appetite).* Annual security validation for all business associates.* Contractual requirements for 24-hour breach notifications.* Executive reporting (monthly dashboards and board-level briefings).* Compliance Lifecycle Acceleration: Implementation timelines are being compressed, requiring more agile compliance processes:* Previous Cycle: * Risk analysis - Biannual* Security training - Annual* Policy updates - Event-driven* 2024 Proposed Rule changes: * Risk analysis - Continuous monitoring + annual formal review* Security training - Quarterly + post-incident refreshers* Policy updates - Annual review + change-triggered updates 3. Technical Implementation Roadmap:* Phased Control Deployment: For resource-constrained organizations, a phased approach is recommended:* Phase 1 (0-6 months): Gap analysis, MFA implementation, enterprise encryption.* Phase 2 (6-12 months): Asset inventory, penetration testing, and network segmentation.* Phase 3 (12-18 months): GRC platform integration, automated vendor risk assessments, continuous monitoring.* Cost Optimization Strategies:* Leverage compliance-as-a-service: MSP partnerships, cloud-based encryption.* Automate documentation: Tools generating audit-ready reports and AI-assisted policy creation.* Pool resources: Join healthcare ISACs and collaborate on training.4. Operationalizing Cultural Change:* Leadership Engagement Tactics: Map HIPAA requirements to business outcomes (e.g., reduced insurance premiums) and implement cross-functional governance committees.* Staff Enablement Programs: Role-based compliance dashboards, gamified training, and recognition programs for control improvement suggestions.5. Anticipating Future Regulatory Trends:* Emerging Requirements: Anticipate requirements related to AI governance, Software Bill of Materials (SBOM) adoption, and Zero Trust architecture.* Strategic Preparation Steps: Conduct tabletop exercises, allocate a budget for adaptive controls, and bui

The Importance of Data Security Posture Management for SMB Leaders
Embracing the Importance of Data Security Posture Management (DSPM) for SMB Tech, Cyber, and Business LeadersIn today’s digital-first world, data is the lifeblood of every organization, including small and medium-sized businesses (SMBs). However, with the increasing adoption of cloud services, artificial intelligence (AI), and remote work environments, managing data security has become more complex. Data Security Posture Management (DSPM) is emerging as a critical solution for modern businesses to protect sensitive information, ensure compliance, and mitigate risks.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.Why DSPM Matters for SMBsDSPM is essential for SMBs because it provides comprehensive visibility into where sensitive data resides, whether on-premises, in the cloud, or across SaaS platforms. This level of insight is particularly valuable for smaller organizations that often face challenges with shadow IT and data sprawl. By understanding where their data lives, SMBs can better manage it and reduce risks associated with unknown or unprotected assets.Another critical benefit of DSPM is its ability to identify and mitigate risks proactively. It continuously monitors data access and usage patterns to detect vulnerabilities such as misconfigurations or over-permissive access controls. For SMBs operating with limited security resources, this proactive approach ensures that potential issues are addressed before they escalate into costly breaches.DSPM also simplifies compliance efforts by mapping regulatory requirements to an organization’s data policies. For SMBs that must adhere to regulations like GDPR, HIPAA, or PCI DSS, DSPM automates many processes involved in audits and reporting. This reduces the burden on internal teams and ensures compliance gaps are identified and resolved efficiently.From a financial perspective, DSPM offers cost efficiency by reducing the likelihood of data breaches. This provides an invaluable safeguard for SMBs that may struggle to recover from the economic and reputational damage caused by such incidents. Additionally, it enables secure collaboration by ensuring that sensitive data is only accessible to authorized users without disrupting workflows—an essential feature for businesses aiming to balance security with operational efficiency.Comparison of Leading DSPM ToolsHere’s a summary of some notable DSPM tools, including Microsoft Purview and other competitors:* Microsoft Purview is a strong choice for organizations already embedded in the Microsoft ecosystem. It integrates seamlessly with Microsoft 365 and Azure environments and offers advanced features like insider risk management and dynamic reporting. However, its effectiveness diminishes for businesses outside the Microsoft ecosystem or those using non-Azure platforms.* Varonis DSPM excels in automated risk remediation and insider threat detection while supporting multi-cloud environments. Its robust capabilities make it a good fit for SMBs looking for a comprehensive solution. However, it less emphasizes cloud-native environments and may require hands-on setup expertise.* CloudDefense.AI offers real-time monitoring and robust compliance automation features that are scalable for growing businesses. While its capabilities are impressive, initial setup can be challenging for teams without specialized knowledge, and new users may experience a steep learning curve.* Prisma Cloud by Palo Alto Networks provides comprehensive support for cloud-native environments and includes prebuilt classifiers for identifying sensitive data. Despite its strengths, its high cost may be prohibitive for smaller organizations, and scanning performance can slow down in larger cloud systems.* Securiti DSPM is particularly well-suited for compliance-heavy industries due to its extensive support of regulatory frameworks. However, its feature-rich platform can be overwhelming for smaller teams, and more effective improvements could be made in scanning unstructured data.How SMB Leaders Can Leverage DSPMTo successfully implement DSPM, SMB leaders should begin by conducting thorough discovery processes to identify all sensitive data across their organization’s environments. This includes structured data like databases and unstructured data stored in SaaS applications or cloud platforms. Understanding where sensitive information resides is the foundation of any effective DSPM strategy.Once discovery is complete, leveraging AI-driven classification capabilities to categorize data based on sensitivity levels, such as personally identifiable information (PII) or protected health information (PHI) is crucial. Automating this process minimizes human error while ensuring consistent application of security policies across all environments.Continuous monitoring should also be prioritized to detect real-time unauthorized access or suspiciou

The Future of Cybersecurity for SMBs: Trends to Watch
The digital landscape is evolving rapidly, posing greater cybersecurity challenges for small and medium-sized businesses (SMBs). In 2024, 94% of SMBs reported experiencing cyberattacks—a sharp increase from 73% the year before. Despite limited resources, SMBs are prime targets due to perceived vulnerabilities. This guide explores critical cybersecurity trends shaping the SMB environment and actionable steps businesses can take to mitigate risks.Investing in robust cybersecurity strategies is not just about preventing attacks—it’s about safeguarding business continuity, customer trust, and long-term profitability. By staying ahead of emerging threats and implementing effective security measures, SMBs can reduce downtime, avoid costly breaches, and maintain a competitive edge in an increasingly digital economy.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.Key Cybersecurity Trends for SMBs1. Ransomware EvolutionRansomware-as-a-Service (RaaS) platforms are becoming more accessible, targeting businesses with fewer than 1,000 employees. With 82% of such companies already in the crosshairs, SMBs must adopt multi-layered defenses.Implementing ransomware protection ensures business continuity by minimizing operational disruptions and safeguarding sensitive data from extortion attempts.Actionable Takeaway: Implement advanced endpoint protection, regular backups, and ransomware-specific incident response plans.2. Cloud Security ChallengesAs more SMBs migrate to the cloud, misconfigurations and incomplete data deletion pose serious risks. Unsecured cloud storage can expose sensitive data.Securing cloud environments enables scalable business operations while protecting critical business assets and customer information.Actionable Takeaway: Conduct regular cloud configuration audits, enforce strict access control policies, and adopt Zero Trust security models.3. AI-Enhanced ThreatsCybercriminals increasingly leverage AI for more sophisticated attacks. Deepfakes for business impersonation and AI-driven phishing campaigns are on the rise.Staying ahead of AI-driven threats protects brand reputation and prevents financial and legal repercussions associated with data breaches.Actionable Takeaway: Invest in AI-powered threat detection tools, continuously train staff on spotting AI-driven scams, and update phishing simulations regularly.Strategic Cybersecurity Focus AreasIn a world where cyber threats evolve daily, SMBs must focus on key cybersecurity areas that deliver both immediate and long-term protection. The following strategic focus areas are foundational pillars that enable businesses to defend against modern cyber risks while aligning with broader organizational goals.Adopting a strategic cybersecurity approach helps SMBs enhance operational resilience, reduce financial and reputational risks, and ensure compliance with industry standards. By addressing these key areas, SMBs can transform cybersecurity from a reactive expense into a proactive investment that drives business success.1. Essential Security MeasuresRobust security measures form the foundation of any effective cybersecurity strategy. SMBs must adopt comprehensive and proactive approaches to safeguard their digital assets. This includes technical safeguards, system maintenance, and policy enforcement that collectively create a resilient security posture.* Multi-Factor Authentication (MFA): Strengthen access controls by requiring multiple verification methods, reducing the risk of unauthorized access.* Regular Updates & Patches: Keep all systems, applications, and devices up-to-date with the latest patches to fix known vulnerabilities and reduce exposure to cyber threats.* Endpoint Protection: Implement advanced endpoint protection solutions to detect, prevent, and respond to cyber threats targeting connected devices.By enforcing these security measures, SMBs can minimize vulnerabilities, improve incident response capabilities, and ensure data integrity, ultimately reducing potential business disruptions and fostering a secure operational environment.2. Employee Security AwarenessCybersecurity is only as strong as its weakest link, and employees often represent the first line of defense against cyber threats. Building a culture of security awareness through continuous training and clear policies can significantly reduce human-error-driven breaches.* Phishing Recognition Training: Conduct quarterly simulated phishing tests to help employees recognize and report suspicious emails, links, and attachments.* Remote Work Security: Enforce secure remote work protocols, including VPNs, encrypted devices, and secure communication tools.* Security Awareness Campaigns: Promote ongoing staff education through workshops, newsletters, and interactive modules that cover emerging threats and best practices.* Incident Reporting Protocols: Establish clear pr

Enhancing Cybersecurity for SMBs: Key Metrics That Matter
Discover essential cybersecurity metrics that can enhance the security posture and resilience of small and medium-sized businesses (SMBs) in a rapidly evolving digital landscape. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Understanding the Cybersecurity Insurance Landscape for SMBs
An essential guide for SMBs to navigate cybersecurity insurance, covering key components, types, costs, and tips for selecting the right policy. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Crafting a Robust Cybersecurity Budget for Small Businesses
Cybersecurity protects digital assets, your business's reputation, and operational continuity. Recent trends reveal that nearly half of all cyberattacks target SMBs. The consequences of inadequate cybersecurity include data breaches, financial losses, and erosion of customer trust. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
NetFlow Analysis: A Game-Changer for SMB Network Security and Efficiency
Small and medium-sized businesses (SMBs) often struggle with network security. The landscape can feel overwhelming, especially with limited budgets, constrained resources, and the need to wear multiple hats. Many SMBs view advanced security tools as out of reach and reserved for large organizations with expansive budgets and dedicated teams. However, NetFlow is a hidden gem within reach of most businesses.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.NetFlow is like having a security camera on your network. Still, instead of capturing visual data, it records the conversations happening within your network—who’s talking to whom, when, and what information is being exchanged. This network protocol collects IP traffic data flowing through your routers and switches, allowing you to monitor and analyze your network in real-time. With the right tools, NetFlow transforms this data into actionable insights, allowing you to proactively identify unusual patterns and address potential threats.Imagine a scenario where your business experiences a sudden website crash. This might be due to a Distributed Denial of Service (DDoS) attack. NetFlow analysis can help you detect such attacks early by identifying unusual traffic spikes from malicious IP addresses, enabling you to mitigate the threat before it disrupts your operations. Similarly, NetFlow can highlight subtle signs of data breaches, like unusual data transfers to unknown locations, even during off-hours.One of NetFlow's most compelling aspects is its accessibility for SMBs. Unlike many high-cost solutions, NetFlow leverages existing network infrastructure, making it cost-effective. Most modern routers and switches already support it, so there’s no need for expensive hardware upgrades.Beyond security, NetFlow offers operational benefits. It provides insights into bandwidth usage, application performance, and network bottlenecks, enabling you to optimize your network and plan for future growth. Additionally, its ability to integrate seamlessly with tools like Security Information and Event Management (SIEM) systems creates a unified security ecosystem, enhancing threat detection and response.For SMBs looking to get started with NetFlow, the first step is to assess your network infrastructure for compatibility. Begin by monitoring critical network segments, such as servers with sensitive data, and invest in training for your IT team to ensure they can interpret NetFlow data effectively. Consider your specific security and operational goals when choosing a tool that balances functionality, ease of use, and affordability.NetFlow empowers SMBs to improve their security, enhance network performance, and gain a competitive edge. It’s an essential tool in today’s cybersecurity landscape—powerful, accessible, and transformative. The journey begins with a single step: check your infrastructure, train your team, and start leveraging NetFlow's power.A Caveat for SMBs Using Cloud ServicesFor SMBs relying heavily on cloud services or Infrastructure as a Service (IaaS) platforms, NetFlow analysis might not fully apply. Many cloud providers do not offer granular access to traffic flow data at the level required for NetFlow analysis. Instead, these organizations might need to rely on the cloud provider’s monitoring tools and security features. If this applies to you, it’s essential to understand what visibility and controls your cloud provider offers and explore complementary solutions.Thanks for reading SMB Tech & Cybersecurity Leadership Newsletter! If you found value in this post, feel free to share it.Product shoutout: TenableCPF Coaching Recommends Tenable for your vulnerability scanning needs. Proactive vulnerability management is crucial to your organization's healthy hygiene.Check it out here: https://shop.tenable.com/cpf-coachingCyvatar.aiHow often do you track the maturity of your program or the implementation status of your controls? As an SMB, it can sometimes be hard to access cybersecurity assessments and tooling; here is a self-assessment tool that you can use to see where your business stands.If you are looking for a security resource to help guide you through the assessment or the maturation of your security program.See where your program scores https://cyvatar.ai/cybersecurity-self-assessment/?via-rr=CHRISTOPHE77 This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Maximizing Cybersecurity for SMBs: The Power of Alerting Systems
Maximizing Cybersecurity for SMBs: The Power of Alerting SystemsAs a senior cybersecurity leader and advisor, I've witnessed firsthand the evolving landscape of digital threats facing small and medium-sized businesses (SMBs). In today's interconnected world, cybersecurity is no longer a luxury but a necessity for businesses of all sizes. The rapid digitalization of operations, coupled with the increasing sophistication of cyber attacks, has made it imperative for SMBs to implement robust security measures. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Essential Cybersecurity Tips for Small Businesses in 2024
Cybercriminals are progressively targeting small businesses. Implementing strong cybersecurity measures is essential to safeguarding your business. This guide provides a thorough overview of how to help protect your small business from cyber threats in 2024. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Securing Remote Workforces: Best Practices for SMBs
Learn the best practices for securing remote workforces, including implementing strong security policies, enhancing team-wide cybersecurity, and securing home networks. Protect your SMB from cyber threats with these expert insights.Subscribe for future episodes! This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Enabling SMBs to understand and address Insider Threats in their businesses
Small and Medium-sized Businesses (SMBs) face numerous security challenges, with insider threats ranking among the most damaging but often undiscussed; with the right strategies and a proactive approach, these threats can be effectively mitigated. Insider threats arise from individuals within an organization who abuse their access to sensitive information or systems for unauthorized purposes and harm the company, intentionally or unintentionally. These threats can lead to data breaches, financial losses, reputational damage, and operational disruptions. Unlike external cyber-attacks, insider threats are more challenging to detect because the individuals involved already have authorized access to sensitive resources. Let's explore the growing concern of insider threats in SMBs and offer practical strategies to mitigate them, with the potential for success and a more secure future for your business.1. Introduction to Insider Threats in SMBsDefining Insider ThreatsAn insider threat occurs when someone authorized access to a company's systems and data misuses that privilege, maliciously or unintentionally, to harm the organization. This threat can come from current or former employees, contractors, or business partners with legitimate access to sensitive resources. In small and medium-sized businesses (SMBs), insider threats are particularly worrisome because these businesses often have fewer layers of security than larger enterprises. Employees in SMBs may have broader access to systems, which increases the risk of misuse. Insider threats can significantly impact a company's success, leading to severe consequences such as data breaches, financial losses, reputational damage, and operational disruptions. Whether the intent is to steal data, sabotage operations, or unintentionally expose sensitive information, the effects of insider threats can be devastating.The Growing Concern for SMBsRecent cybersecurity reports, such as one from the Ponemon Institute, indicate that insider threats have grown by nearly 50% over the past few years. This trend is alarming, particularly for SMBs, which often lack the sophisticated security infrastructure of larger organizations. These larger organizations might have dedicated security teams, advanced threat detection systems, and regular security audits, which SMBs may need more resources to implement. The smaller teams and limited resources of SMBs make it challenging to implement comprehensive security measures, leaving them more vulnerable to insider attacks. Additionally, SMBs may only sometimes have dedicated IT staff to monitor security threats in real-time. With the rise of remote work and increased digital reliance, insider threats are becoming an even more pressing issue for small businesses.2. Mitigating Employee-Related RisksIdentifying Potential RisksThe first step in addressing insider threats is identifying the potential risks that employees may pose. Common risk factors include disgruntled employees who may be motivated to harm the business, accidental data leaks due to negligence, and weak access control policies that give too much access to sensitive information. SMBs can reduce these risks by employing behavioral monitoring technologies that track abnormal employee activities. For example, unusual login times, unauthorized file access, or abnormal data transfers can serve as red flags. Identifying these risks early on enables SMBs to take proactive steps before damage occurs.Implementing Preventative MeasuresSmall and medium-sized businesses (SMBs) need to establish and enforce strong preventive measures to minimize the risk of insider threats. Implementing strict access control policies is one of the most effective methods for protecting sensitive data. These policies should follow the principle of least privilege, meaning that employees should only have access to the data and systems necessary for their specific roles. This principle ensures that even if an employee's credentials are compromised, the potential damage is limited to the data and systems they access, reducing the overall risk. It's crucial to regularly review and update these access controls to prevent employees from retaining unnecessary permissions after role changes. Additionally, businesses need to conduct thorough background checks on new hires, closely monitor employee activities for any signs of suspicious behavior, and ensure the encryption of sensitive data to prevent unauthorized access.3. Insider Threat Identification TechniquesBehavioral Monitoring TechnologiesBehavioral monitoring technologies are crucial in identifying insider threats; these technologies monitor and analyze employee activities, including email communications, network access, file transfers, and login patterns. For instance, sudden access to large volumes of sensitive data or downloading files outside of regular business hours could indicate an insider threat. However, small and medium-sized businesses (SMBs) must b

Understanding and Mitigating Phishing Attacks in SMBs
Phishing attacks pose a growing threat to Small and Medium Businesses (SMBs), targeting their sensitive data and financial resources. These deceptive tactics, often delivered through fraudulent emails, trick employees into revealing confidential information or unknowingly downloading malware. For SMBs, the impact of a successful phishing attack can be devastating, leading to significant financial loss, data breaches, and reputational damage. In this guide, we'll explore the rising danger of phishing and the importance of solid email security. We'll also provide actionable strategies to protect your business from these increasingly sophisticated threats.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.1. Introduction to Phishing Attacks in SMBsPhishing attacks have significantly threatened Small and Medium Businesses (SMBs). These attacks involve malicious actors sending deceptive emails to trick recipients into revealing sensitive information. The impact on SMBs can be severe, leading to financial loss, data breaches, and reputational damage. Recent statistics show a sharp rise in phishing attacks targeting SMBs, highlighting the need for robust security measures.Email security is crucial in protecting SMBs from phishing attacks. Without proper safeguards, businesses are vulnerable to various email security threats such as malware, ransomware, and spear-phishing. Ensuring robust email security helps prevent unauthorized access and protects sensitive information.This guide educates readers on phishing prevention, threat identification, and effective response strategies. By the end, you will have a comprehensive understanding of how to protect your SMB from phishing attacks.2. Phishing Prevention StrategiesImplementing robust email security measures is one of the first steps in phishing prevention. These include using email filters and spam detection tools to identify and block suspicious emails. Secure email gateways add another layer of protection by inspecting inbound and outbound emails for threats.It is crucial to train employees to recognize phishing attempts. Regular updates and simulated phishing exercises can help employees stay vigilant. Teaching them to look for red flags, such as suspicious links and unfamiliar senders, can significantly reduce the risk of falling for phishing scams.Crafting clear policies on email use and security is essential. These policies should outline acceptable email practices and procedures for reporting suspicious emails. Regular audits and compliance checks ensure guidelines are followed and updated.3. Identifying Phishing ThreatsUnderstanding common phishing tactics is critical to identifying threats. Phishing emails often contain urgent messages prompting immediate action, such as clicking a link or providing personal information. Differentiating between phishing and spear-phishing attacks, which are more targeted, is also essential.Utilizing AI and machine learning can enhance threat detection. These technologies analyze email patterns and flag suspicious activities. Integrating threat intelligence feeds into your security infrastructure provides real-time updates on emerging threats.Continuous monitoring is vital for identifying phishing threats promptly. Tools and software that offer 24/7 monitoring ensure that any suspicious activity is detected and addressed immediately. This proactive approach helps in mitigating potential damage.4. Developing Effective Response StrategiesOnce a phishing attempt is identified, immediate action is required. Isolating affected systems prevents the spread of malicious software. Following a predefined response plan is crucial to minimize damage and secure your network.Informing stakeholders and affected parties is critical in managing a phishing incident. Transparent communication helps maintain trust, and managing public relations effectively ensures that your business reputation remains intact.After addressing the immediate threat, reviewing and revising security measures is essential. Conducting a post-mortem analysis helps identify weaknesses and prevent future attacks. Implementing lessons learned ensures continuous improvement in your security posture.5. Attack Simulation and Continuous ImprovementRegular phishing attack simulations prepare your team for real threats. These simulations help identify vulnerabilities and improve response strategies. They also provide valuable insights into how employees react to phishing attempts.Continuous improvement is vital for maintaining strong security measures. Regular updates and enhancements based on simulation results ensure your defenses remain effective. Encouraging a culture of constant learning and adaptation keeps your team prepared for evolving threats.Collecting and analyzing user feedback is crucial for refining training and security protocols. This feedback h
Enabling a SMB Security with Log Analysis and SIEM
The Business Value of Log Analysis and SIEM for SMBsAs threats become more sophisticated, robust security measures are paramount, even for small-medium businesses. One critical component of a comprehensive security strategy is log analysis and Security Information and Event Management (SIEM). These tools allow SMBs to detect potential threats early, allowing for timely intervention and mitigation. Log analysis involves reviewing and interpreting logs generated by computers, networks, and applications. These logs capture a wide range of activities, from user actions to system errors, providing invaluable insights into the health and security of IT environments. SIEM systems take this further by centralizing log data from multiple sources, correlating events, and providing real-time analysis to detect and respond to security incidents. For SMB leaders and security teams, investing in log analysis and SIEM can significantly enhance threat detection capabilities, improve compliance, and optimize operational efficiency.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.Log analysis is the foundation of effective cybersecurity, providing invaluable insights into the activities occurring within an organization's IT infrastructure. Businesses can uncover patterns, anomalies, and potential security incidents that might go unnoticed by meticulously examining log files generated by various systems, applications, and network devices. SIEM systems take this further by aggregating and correlating data from multiple sources, offering a holistic view of an organization's security posture and enabling real-time threat detection and response.Tasks and Organizational ValueImplementing log analysis and SIEM can transform how SMBs manage their cybersecurity efforts. These solutions go beyond mere security enhancements; they contribute to operational efficiency, regulatory compliance, and overall business resilience.* Real-time Threat Detection: By continuously monitoring logs, SIEM systems can identify suspicious activities, such as unauthorized access attempts or unusual network traffic patterns. This allows businesses to respond quickly, minimizing potential damage from cyber threats.* Compliance and Reporting: Many industries have strict regulatory requirements for data security and privacy. Log analysis helps ensure compliance by providing detailed audit trails and reports that can be used to demonstrate adherence to regulations like GDPR or HIPAA.* Operational Efficiency: Log analysis tools automate the collection and parsing of log data, reducing the manual effort required by IT teams. This saves time and allows staff to focus on more strategic initiatives, improving overall productivity.Current Challenges and SolutionsDespite the clear benefits of implementing log analysis, SIEM systems, and partnering with MSSPs, SMBs often encounter significant challenges in adopting and optimizing these solutions. These obstacles range from resource constraints to the sheer complexity of modern cyber threats, creating a landscape that can be daunting for businesses with limited IT and security resources.* Resource Constraints: Limited budgets and personnel can make it difficult for SMBs to deploy and maintain sophisticated SIEM systems. To address this, businesses can explore open-source or cloud-based services that offer scalability and cost-effectiveness.* Data Overload: The sheer volume of log data can be overwhelming, leading to alert fatigue and potential oversight of critical incidents. Effective log management strategies, such as data filtering and prioritization, can help manage this influx and ensure that only relevant alerts are escalated.* Complexity of Integration: Integrating SIEM systems with existing IT infrastructure can be complex. Choosing solutions with user-friendly interfaces and robust support can ease this process, ensuring seamless integration and operation. Partnering with a Managed Security Service Provider could be another avenue to consider.Optimizing with Future SolutionsAs the cybersecurity landscape evolves, so must the strategies and tools used to protect digital assets. The future of log analysis, SIEM systems, and managed security services holds exciting possibilities for enhancing threat detection, streamlining operations, and improving overall security postures.* Leverage AI and Machine Learning: Incorporating AI and machine learning into log analysis can enhance threat detection by identifying patterns and anomalies that traditional methods might miss. These technologies can also automate responses, reducing the time to mitigate threats.* Adopt a Zero Trust Model: Implementing a Zero Trust security framework can complement log analysis efforts by ensuring all access requests are verified and monitored, regardless of origin. This approach enhances security by minimizing the risk of in

Enhancing Threat Detection in SMBs: A Guide to NIST CSF Detection Capabilities
Understanding the Importance of Threat Detection in SMBsSmall and medium-sized businesses are increasingly vulnerable to cyber threats. To effectively scale and innovate, they must insert cybersecurity mechanisms that secure their assets and data for their customers. In any robust cybersecurity strategy, threat detection certainly needs to be included. This goes above traditional monitoring by hunting for potential threats across all planes of business operations: data, control, and identity. It is in these broad areas that the leaders of SMBs can make a difference in the detection capabilities of the NIST Cybersecurity Framework and provide a more secure environment for their business.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.The Role of Data, Control, and Identity PlanesIn cybersecurity, understanding the different planes of business operations—data, control, and identity—is crucial for effective threat detection. Each plane represents a unique aspect of your business's digital ecosystem that requires specific attention and strategies to safeguard against potential threats. By focusing on these planes, SMB leaders can develop a more comprehensive approach to threat detection that aligns with the NIST Cybersecurity Framework (CSF). This section will explore the significance of each plane and how they contribute to a robust cybersecurity posture.Data Plane: The data plane involves processing, storing, and transmitting data within a business. Effective threat detection ensures that sensitive information is safeguarded against unauthorized access and breaches. Here's where advanced data monitoring tools come in. These tools can help identify unusual patterns or anomalies that may indicate a cyber threat, giving you the reassurance that you're one step ahead in protecting your business.Control Plane: The control plane includes the systems and processes that manage data flow and access within the organization. Threat detection here focuses on ensuring that only authorized personnel have access to critical systems and data. By monitoring control plane activities, businesses can prevent unauthorized changes and detect potential insider threats, keeping you vigilant and aware of potential risks.Identity Plane: The identity plane pertains to the authentication and authorization of users accessing business systems. Effective threat detection in this plane involves monitoring user activities and ensuring robust access controls. Implementing multi-factor authentication and identity management solutions can significantly reduce the risk of identity-based attacks.Examples of Threat Detection Tasks and Their ValueImplementing threat detection capabilities involves various tasks that, when executed effectively, can significantly enhance an organization's security posture. From continuous monitoring to anomaly detection, these tasks are designed to identify and mitigate potential threats before they can cause harm. Understanding the value of these tasks helps build a resilient cybersecurity strategy and demonstrates the tangible benefits to stakeholders. This section will delve into specific threat detection tasks and highlight their importance to your organization.* Continuous Monitoring: By continuously monitoring network traffic and user activities, businesses can quickly identify and respond to potential threats. This proactive approach helps minimize the impact of cyber incidents and ensures business continuity.* Anomaly Detection: Machine learning algorithms can be utilized to detect anomalies in data and user behavior, providing early warnings of potential threats. This allows businesses to address vulnerabilities before attackers exploit them.* Incident Response Planning: Developing and regularly updating an incident response plan ensures businesses are prepared to handle cyber incidents effectively. This reduces downtime and mitigates the financial and reputational impact of breaches.Current Environmental Challenges and Overcoming ThemThe cybersecurity landscape constantly evolves, presenting SMBs with many challenges in implementing effective threat detection strategies. Limited resources, a shortage of skilled personnel, and the ever-changing nature of cyber threats are just a few hurdles businesses must overcome. However, with the right approach and tools, these challenges can be transformed into opportunities for strengthening security measures. This section will discuss the challenges SMBs face and provide insights into overcoming them to build a more secure business environment.SMBs face several challenges in implementing effective threat detection strategies, including limited resources, lack of expertise, and evolving threat landscapes. To overcome these challenges, businesses can:* Leverage Managed Security Services: Partnering with managed security service providers (MSSPs) can pr

Enhancing Security in Open-Source Code for SMBs
In the digital world today, it is more often than not that small and medium-sized businesses are found turning to open-source code and public software repositories to be able to build and enhance their technological capabilities. On one hand, such resources bring about considerable cost savings and advantages of innovation, but on the other hand, they also bear the potential security risks that might compromise the integrity of business operations. It is against this backdrop that, as a senior cybersecurity leader and advisor, I come forth to place emphasis on the security and integrity of open-source code and how SMB leaders and security teams can effectively deal with these risks.SMB Tech & Cybersecurity Leadership Newsletter is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.Open-source software has become a cornerstone for many businesses, providing a flexible and cost-effective way to access cutting-edge technology. However, the very nature of open-source code—its openness and collaborative development—can also make it a target for malicious actors seeking to exploit vulnerabilities. For SMBs, which may lack the extensive resources of larger enterprises, the challenge is to harness the benefits of open-source software while mitigating the associated risks. By prioritizing security and integrity in open-source code, SMBs can protect their assets, maintain customer trust, and ensure business continuity.Examples of Use Cases and their value* Code Review and Vulnerability Assessment: It is crucial to regularly review open-source code for vulnerabilities. This task helps identify potential security flaws before they can be exploited, thereby protecting the organization from breaches and data loss.* Implementing Security Tools: Tools such as static code analyzers and dependency checkers can automate the process of detecting vulnerabilities in open-source components. This not only saves time but also enhances the organization's overall security posture.* Community Engagement and Contribution: Participating in open-source communities lets businesses stay informed about the latest security patches and updates. Contributing to these communities can foster goodwill and collaboration, leading to more robust and secure software solutions.Current Environmental Challenges and SolutionsThe open-source ecosystem is vast and constantly evolving, which presents several challenges:* Rapidly Changing Codebases: Maintaining frequent updates and patches can be daunting. SMBs can overcome this by implementing automated update management systems that ensure the timely application of security patches.* Lack of In-House Expertise: Many SMBs struggle with limited cybersecurity expertise. Partnering with external cybersecurity firms or consultants can provide support and guidance to manage open-source risks effectively.* Supply Chain Vulnerabilities: Software dependencies' interconnected nature can introduce vulnerabilities. Conducting thorough supply chain risk assessments and utilizing tools that map and monitor dependencies can help mitigate these risks.Potential Future SolutionsLooking ahead, SMBs can optimize their approach to open-source security by:* Adopting AI and Machine Learning: These technologies can enhance threat detection and response capabilities, providing real-time insights into potential vulnerabilities and threats.* One possible use case includes the ability to analyze SBOMs, connect software packages to those in use in the environment, and aid with the remediation of patching or updates.* Developing a Security-First Culture: Encouraging a mindset where security is integrated into every aspect of software development and deployment can lead to more secure outcomes. This involves training employees and fostering an environment where security is everyone's responsibility.Actionable SummaryTo effectively manage the security and integrity of open-source code, SMB leaders and security teams should focus on the following action items:* Conduct regular code reviews and vulnerability assessments.* Implement automated tools for detecting and managing vulnerabilities.* Engage with open-source communities for the latest security updates.* Partner with cybersecurity experts to enhance in-house capabilities.* Foster a security-first culture within the organization.By taking these steps, SMBs can leverage the benefits of open-source software while minimizing security risks, ultimately enhancing their resilience in an increasingly digital world.Thanks for reading SMB Tech & Cybersecurity Leadership Newsletter! If you found value from this post, sharing it with others would mean the world to us.Product shout-out: LearnWorldsAt CPF Coaching, we're always on the lookout for top-notch tools that empower our clients to the max. This is why we couldn't, but we are very excited about recommending LearnWorlds. Just recently named "Top User-rated Online Course Plat