
SMB Tech & Cyber Newsletter | CPF Coaching
I empower Chief Information Security Officers (CISOs) and Small to Medium-sized Businesses (SMBs) to elevate their cybersecurity strategies, guiding them past stagnation to achieve tangible outcomes.
CPF Coaching | Christophe Foulon
Show overview
SMB Tech & Cyber Newsletter | CPF Coaching has been publishing since 2022, and across the 4 years since has built a catalogue of 120 episodes. That works out to roughly 20 hours of audio in total. Releases follow a fortnightly cadence.
Episodes typically run under ten minutes — most land between 3 min and 12 min — with run-times ranging widely across the catalogue. None of the episodes are flagged explicit by the publisher. It is catalogued as a EN-language Business show.
There hasn’t been a new episode in the last ninety days; the most recent episode landed 3 months ago. The busiest year was 2024, with 38 episodes published. Published by CPF Coaching | Christophe Foulon.
From the publisher
I empower Chief Information Security Officers (CISOs) and Small to Medium-sized Businesses (SMBs) to elevate their cybersecurity strategies, guiding them past stagnation to achieve tangible outcomes. substack.cpf-coaching.com
Latest Episodes
View all 120 episodes
5 Critical Security Alerts from Last Week: Copilot Bugs, Bluetooth Hacks, and New Privacy Laws
January 2026 Alert: Critical Microsoft Copilot vulnerability (Reprompt), Bluetooth "WhisperPair" exploit affecting Sony/Google devices, and new privacy laws in IN, KY, & RI. Get the executive summary and 30-day mitigation plan for SMBs. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

AI, Identity, and Breaking Into Cyber: CEO Jasson Casey’s Blueprint for Success
From building software to defending it: Jason Casey (CEO, Beyond Identity) shares his journey from Software Engineer to Cybersecurity Expert. Discover why mastering network protocols and engineering fundamentals is the secret to a successful cyber career. Listen now on Breaking into Cybersecurity. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

The Glass House: Why 2026 is the Year We Must Audit Our "Agents" and "Avatars"
CES 2026 changed the threat landscape. From "Superuser" AI agents to "cute" surveillance robots like Mirumi, we outline the top 4 trends SMB tech leaders must address immediately to secure their organizations. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

3 Urgent Cyber Threats Costing SMBs Millions (2025 Update)
Urgent briefing for US SMBs: Critical patches needed for WatchGuard, Fortinet, & Cisco. Discover how to stop AI attacks and avoid $3M breach costs. Read the Urgent briefing for US SMBs: Critical patches needed for WatchGuard, Fortinet, & Cisco. Discover how to stop AI attacks and avoid $3M breach costs. Read the plan. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Don't Boil the Ocean: A Cost-Effective Architecture for CMMC Level 2
CMMC Phase 1 is effective as of Nov 2025. DIB leaders: Get the strategic guide to CUI, VDI, and NIST 800-171 compliance before the 2026 deadline. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

The Silent Kill Switch: Why Your Business Needs a "Human" Disaster Recovery Plan
Is your business one tragedy away from collapse? Learn how to mitigate "Key Person Risk" and the "Bus Factor" with our 2025 guide to IT succession planning. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Your CEO and Your Sales Team Don't Face the Same Threats.
The “One-Size-Fits-All” ProblemWe’ve all been there. A mandatory, hour-long cybersecurity training video that covers everything from phishing to physical security in a bland, generic way. Your marketing team is half-listening while thinking about their next campaign, and your finance department is wondering how any of this applies to their daily invoice processing. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Breaking into Cybersecurity: An In-Depth Conversation with Eric Stride
In the latest episode of “Breaking into Cybersecurity,” host Chris Foulon sits down with Eric Stride, the Chief Security Officer at Huntress. Eric’s journey into cybersecurity is not only inspiring but also enlightening for anyone looking to enter this ever-evolving field. With over two decades of experience in the military and private sectors, Eric shares his insights on career development, leadership, and the future of cybersecurity. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Quantum Computing: Your Next Great Opportunity
Quantum Computing: The Future of Innovation and Security In this episode, we explore the revolutionary impact of quantum computing on the future of technology, innovation, and security. Learn about the key differences between classical bits and quantum qubits, and how superposition and entanglement enable unprecedented computational capabilities. Discover the strategic opportunities quantum computing presents for industries such as pharmaceuticals, logistics, and artificial intelligence, as well as the urgent cybersecurity threats it poses. Finally, gain actionable insights on how to prepare your organization for the quantum age by conducting risk assessments, exploring post-quantum cryptography, and ensuring crypto-agility. Don't be left behind—embrace this transformative technology and secure your place in the future. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
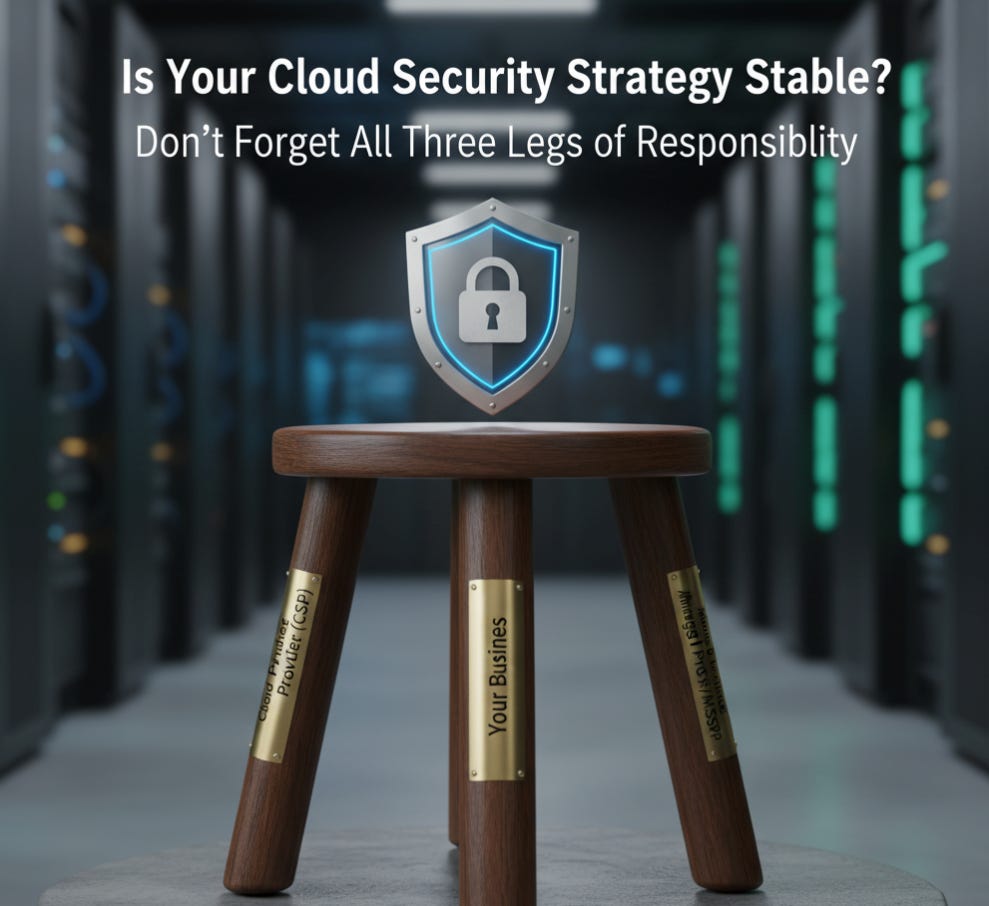
Beyond the Cloud: Mastering the Shared Responsibility Model for Comprehensive Risk Management
Don't assume your cloud provider has you covered. Master the Shared Responsibility Model, build a comprehensive SRM, and align your strategy with frameworks like NIST and CMMC. Read our guide to achieve total accountability. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
Navigating the Future of Cybersecurity: Insights from William (Bill) Welser IV
Discover what lies ahead in cybersecurity with technology expert Bill Welser IV. Gain insights into AI's influence, key skills needed, and ways to prepare for the future. From his experience in the Air Force to AI startups, Bill Welser IV discusses his distinctive cybersecurity career path. Explore topics like systems thinking, new technologies, and advancing your career. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Cybersecurity Entrepreneurship: Real-World Advice from Serial Founder Sinan Eren
By Chris Foulon & Sinan ErenIntroductionIn this episode of "Breaking into Cybersecurity," we sat down with Sinan Eren, a seasoned cybersecurity professional, entrepreneur, and founder. Sinan’s journey from a curious hobbyist in Istanbul to a serial founder in Silicon Valley offers a wealth of insights for anyone interested in cybersecurity, entrepreneurship, or both. Here are the highlights and lessons from our conversation.From Hobbyist to Professional: The Early DaysSinan’s entry into cybersecurity wasn’t a deliberate career choice. In the late 1990s, cybersecurity wasn’t even a defined field—just a function of IT. Resources were scarce, and much of the learning happened in underground communities like IRC and through publications like FRAC magazine. For Sinan, curiosity and a desire to experiment led him to discover vulnerabilities and share his findings on platforms like Bug Track, which eventually opened doors to job opportunities.Key Takeaway: Sometimes, passion and curiosity can be more important than formal education in breaking into a new field.Signature-Based vs. Heuristic Security: A Technical EvolutionSinan explained the shift from signature-based antivirus solutions to heuristic and behavioral approaches. Early security tools relied on known patterns to detect threats, but as malware evolved—like the infamous Code Red worm—this reactive approach proved insufficient. The industry began to focus on detecting abnormal behaviors, setting the stage for modern endpoint security.Key Takeaway: The cybersecurity landscape is always evolving. Staying ahead means understanding both the history and the latest trends in threat detection.Entrepreneurship in Cybersecurity: Two PlaybooksSinan’s entrepreneurial journey followed two main playbooks:* The Hype Playbook: Attach security to the latest technology trend (e.g., AI + Security).* The Next-Gen Playbook: Take an existing solution and make it better, faster, or more secure (e.g., reinventing VPNs with Zero Trust Network Access).His first company focused on mobile security, capitalizing on the rise of mobile apps and their security flaws. Later ventures addressed remote access and automation, always driven by real-world needs and feedback from users.Key Takeaway: Successful startups often solve existing problems in new ways or improve on what’s already out there. Listen to the market and adapt.Lessons Learned: Growth, Pivots, and ExitsSinan shared candid stories about the challenges of scaling a startup, including the risks of over-reliance on a single partner and the importance of diversifying your customer base. He emphasized the value of learning from mistakes and knowing when to pivot or sell.Key Takeaway: Flexibility and self-awareness are crucial in entrepreneurship. Sometimes, the best move is to exit and apply your lessons to the next venture.Automation and the Future: Beyond CybersecuritySinan’s latest venture emerged from listening to managed service providers who struggled with operating and automating a growing stack of security tools. By leveraging process mining, UI automation, and AI, his team built solutions that automate repetitive tasks—not just in cybersecurity, but also in finance and other fields.Key Takeaway: The skills and solutions developed in cybersecurity can often be applied to other industries. Don’t limit your vision to a single domain.Advice for Aspiring Professionals and Leaders* For Beginners: The field is more exciting than ever, especially with the rise of AI and LLMs (Large Language Models). Red teaming and offensive security remain fertile ground for creative minds, regardless of background.* For Experienced Pros: Embrace the challenge of integrating AI responsibly. Focus on building guardrails and understanding business processes, not just deploying tools.* For Entrepreneurs: Understand your customers’ workflows and pain points. Document processes, model workflows, and always be ready to adapt your product or business model.ConclusionSinan Eren’s story is a testament to the power of curiosity, adaptability, and listening—both to technology and to people. Whether you’re just starting out or leading a team, the lessons from his journey can help guide your own path in cybersecurity and beyond.To hear the full conversation, listen to the episode of Breaking Into Cybersecurity (and uploaded as the video in this post ;-) The YouTube channel has years of previous conversations)Some security tools you can consider for improving your business security posture:CrowdStrike Falcon: An AI-driven platform for securing your infrastructure at scale and keeping up with AI advancements. https://crowdstrike2001.partnerlinks.io/Cpf-coachingINE Security Awareness and Training is essential for your team to stay updated with the evolving threat landscape, enhancing the effectiveness of the teams supporting your organization. https://get.ine.com/cpf-coachingTenable helps identify weaknesses in your infrastructure, whether on-premises, in the cl
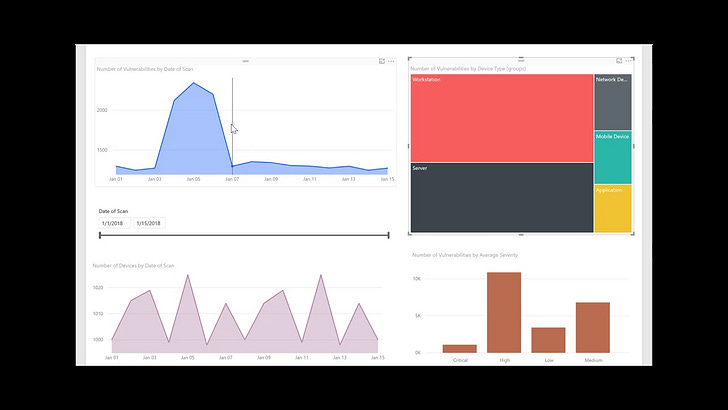
How to Build a Security Culture with Data-Driven Reporting
Foster a true security-first culture by mastering effective cloud security reporting. Learn to translate technical risk into business impact for leadership and technical teams using tools like Microsoft Power BI. Move security from a cost center to a strategic business enabler. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Vulnerability Management Metrics: 15 KPIs to Measure & Mature Your Program
Supercharge your vulnerability management with a data-driven approach! Discover the 15 essential key performance indicators (KPIs) that will help you track your progress, highlight the value of your efforts, and elevate your security program. Embrace actionable metrics to continuously measure, monitor, and enhance your strategy—it's a journey towards a more secure future! This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

The Ghost in Your Cloud: How Hackers Use Social Engineering to Infiltrate and Attack
The Ghost in Your Cloud: How Hackers Use Social Engineering to Infiltrate and AttackUnmasking the "low and slow" identity attacks where threat actors lie in wait within your cloud accounts, and how to fight back before they strike.Discover the new wave of silent cyber threats. Learn how hackers use social engineering to compromise cloud accounts, stay dormant to evade detection, and launch devastating attacks later. Protect your organization now. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Data-Centric Security: Protect Your Cloud Data with Microsoft Defender
Stop chasing every vulnerability. Learn how a Data-Centric Security approach using Microsoft Defender for Cloud helps you discover, classify, and protect your most sensitive cloud data. Prioritize real business risks and prevent impactful breaches. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
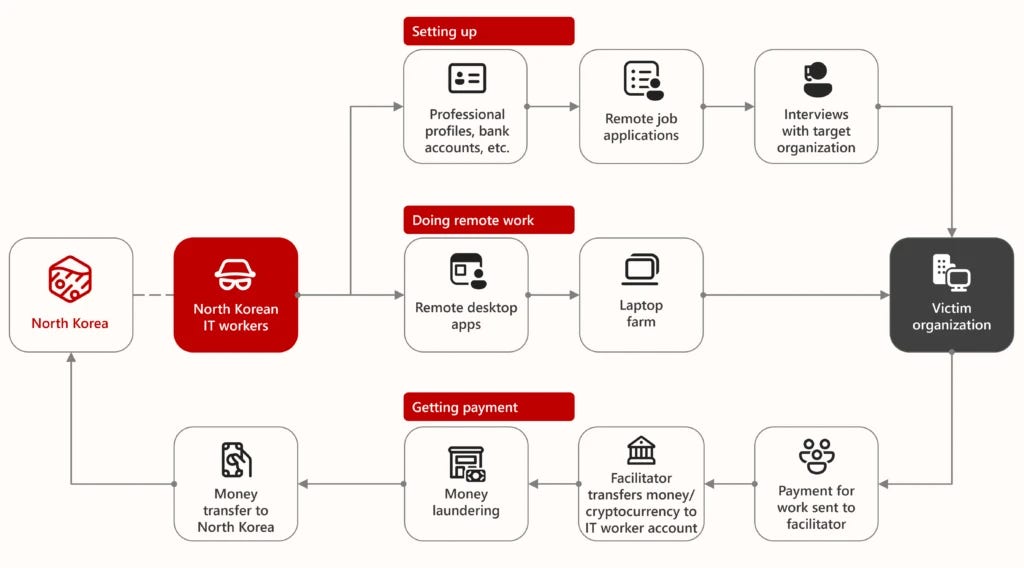
The Phantom Workforce: A Guide to Combating State-Sponsored IT Infiltration
🚀 Transform Your Cybersecurity Approach! 🚀 Join me on a journey through "The Phantom Workforce," where I delve into combating state-sponsored IT infiltration. Equip yourself with knowledge and strategies to protect your organization's sensitive information from modern threats. Let's enhance our cyber defenses together! #cyberawareness #protectyourdata #ITinfiltration This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

Develop and Enforce Robust Remediation Policies and SLAs
Strengthen your organization's security response with robust Remediation Policies and SLAs! Discover how to transform your vulnerability management program into a mature, auditable business function that ensures accountability and timely risk reduction. Learn more about the essential components of a successful policy in our latest discussion. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe

From Psychology to Cybersecurity: Craig Taylor's Impact
In this episode of Breaking into Cybersecurity, host Chris welcomes Craig Taylor, CEO of Cyber Hoot, as he shares his inspiring journey into the cybersecurity industry. Known for his role as a virtual CISO and cybersecurity awareness advisor, Craig discusses how he began his career with a psychology degree and eventually transitioned into cybersecurity. He delves into the importance of positive reinforcement over punishment in cybersecurity training and the evolving role of AI in detecting and mitigating threats. Craig also offers valuable advice for those looking to enter the field and emphasizes the need for organizations to understand and manage AI-related risks. Tune in for insights on cybersecurity, AI advancements, and practical tips to enhance cybersecurity awareness. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe
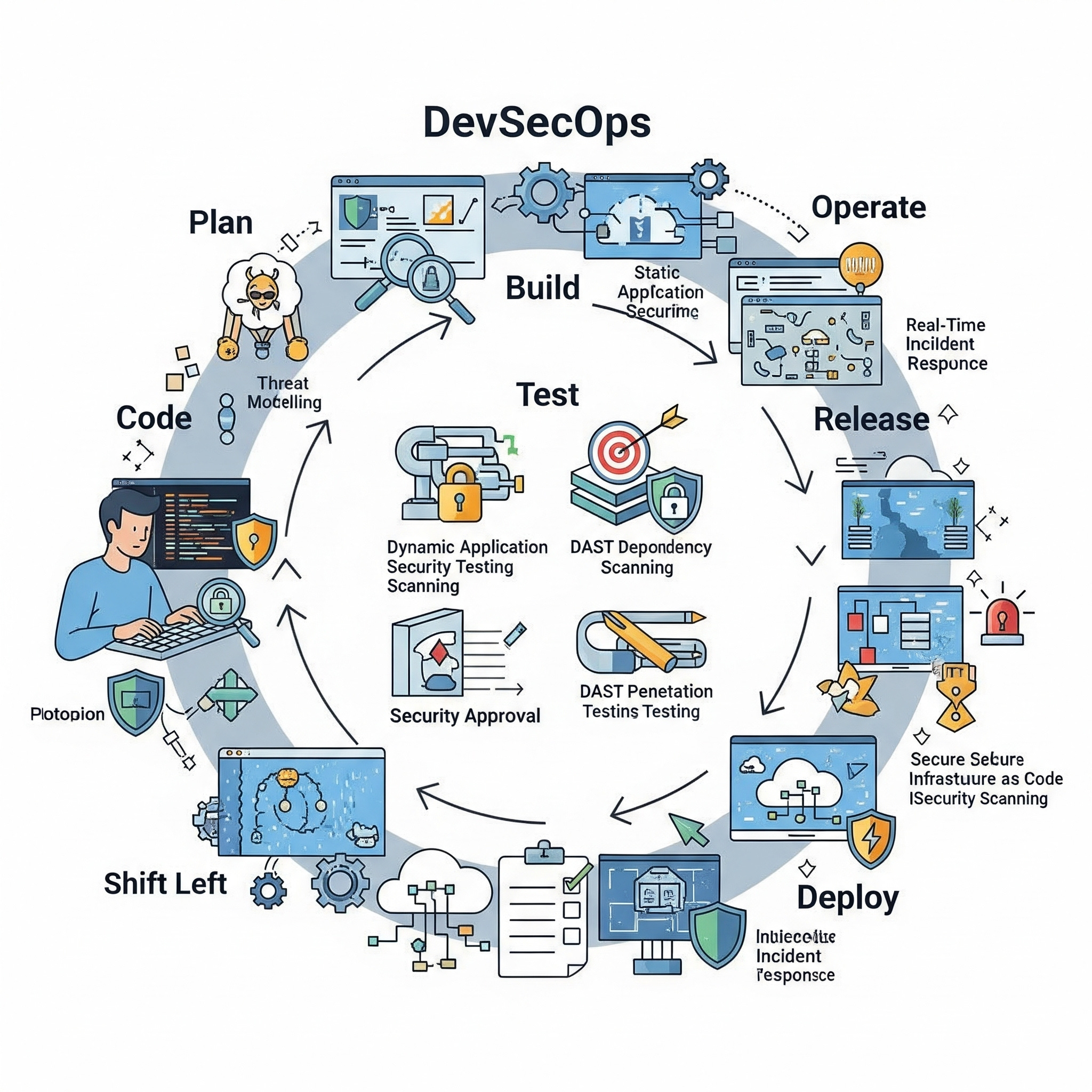
Embed Security into the DevOps Lifecycle (DevSecOps)
Learn to "shift left" with DevSecOps. Discover how to integrate security into your development lifecycle, from Infrastructure as Code (IaC) scanning to container analysis, using Microsoft Defender for Cloud to build a proactive, code-to-cloud security posture. This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit substack.cpf-coaching.com/subscribe