
CISO Insights: Voices in Cybersecurity
464 episodes — Page 4 of 10

Ep 315Trick or Threat: Your Personal Cybersecurity Survival Guide for 2026
Artificial intelligence has fundamentally reshaped the threat landscape, enabling attackers to deploy flawless, context-specific phishing emails and clone the voices of executives, leading to massive losses like the Hong Kong multinational firm that lost $25 million during a deepfake video call scam. With ransomware back on the rise and 77% of CISOs identifying AI-generated phishing as a growing concern, cybercriminals are trading generic lures for high-quality, persistence-based payloads that bypass traditional defenses. We break down the urgent shift required for organizations, from embracing resilient Zero Trust architecture to implementing stringent verification protocols and continuous employee education to survive this era of sophisticated, automated cyberattacks. Sponsor: www.cisomarketplace.com www.cisomarketplace.services podcast.cisomarketplace.com www.microsec.tools www.threatwatch.news

Ep 314The Digital Hustle: RaaS, EDR Killers, and the Cybercrime Business Model
RaaS (Ransomware-as-a-Service) has professionalized cybercrime, turning digital extortion into a resilient business where affiliates leverage sophisticated toolkits for high-stakes attacks on critical sectors. This episode details how threat actors circumvent defenses by compromising high-value systems like VMware ESXi hypervisors and Managed File Transfer solutions, and by utilizing EDR Killers to execute malicious actions undetected. We explore the necessary response, which involves employing advanced behavioral analysis, multi-factor authentication (MFA), network segmentation, and automated playbooks to dismantle the entire criminal supply chain. Sponsor: www.cisomarketplace.com

Ep 313Speaking 'Boardish': A CISO's Guide to Risk, Resilience, and Revenue
The modern Chief Information Security Officer (CISO) role is evolving from a purely technical function to an enterprise risk leadership position, yet many leaders struggle to secure necessary resources due to a fundamental communication gap with the board. This podcast explores how security executives can master "Boardish"—the language of finance, strategy, and governance—by translating critical threats like ransomware and AI exposure into clear, actionable, financial, and business consequences. We share strategies to elevate security from a mere compliance checkbox to a business enabler, focusing on measuring cyber resilience and quantifying investment returns based on risk reduction to secure vital board support. Sponsor: www.cisomarketplace.com www.cisomarketplace.services

Ep 312When Trust Breaks: Auditing the $300M Third-Party Liability Cap
Third-party relationships expose organizations to major threats across operational, strategic, and legal risk areas, including the significant danger of reputational damage and the potential for loss of intellectual property. Recent managed service provider (MSP) cyberattacks have resulted in catastrophic financial devastation, demonstrating that an organization cannot escape blame when a vendor fails. We analyze essential contractual controls—such as clear termination conditions, robust indemnification clauses, and the critical right to audit—that serve as the foundational mechanism for mitigating catastrophic liability exposure. Sponsors: www.cisomarketplace.com https://vrm.cisomarketplace.services

Ep 311Resilience in an AI-Accelerated World: The CISO's Objective Challenge
This episode tackles the CISO's strategic mandate: moving beyond subjective assessments, as "Security without true adversarial testing is just an illusion," to achieve objective measurement and resilience. We analyze key vulnerability trends, including the significant surge in hardware, API, and broken access control flaws, recognizing that every AI advance makes the security landscape exponentially more complex for attackers still targeting foundational layers. Learn how continuous, community-powered red teaming serves as the crucial diagnostic stress test required to validate defense effectiveness, translate technical risks into compelling board narratives, and ultimately drive demonstrable security outcomes. Sponsors: www.cisomarketplace.com www.cisomarketplace.services

Ep 310The Hybrid SOC Revolution: AI, ATT&CK, and Fortifying Resilience in 2025
Cyber threats are evolving at an unprecedented pace, with sophisticated ransomware and supply chain breaches on the rise, contributing to cybercrime costs estimated to exceed $10.5 trillion per year by 2025. We delve into the optimal hybrid SOC model, discussing how organizations leverage AI-driven automation to reduce Mean Time to Detect (MTTD) by up to 40% and align defenses using the MITRE ATT&CK framework. Learn why critical gaps in lateral movement and impact detection, coupled with underfunding training (only 20% of SOC budgets), remain persistent challenges that security leaders must address to transition from reactive to predictive defense. https://cisomarketplace.services/ciso-calendar https://www.scamwatchhq.com/scammer-calendar-a-year-round-guide-to-scams-and-their-peak-times Sponsors: www.cisomarketplace.services www.scamwatchhq.com

Ep 309The Trust Trap: Why Employees Turn Malicious and How Causal AI Predicts the Breaking Point
Insider threats are not just technical breaches but fundamentally human failures, where employees exploit their legitimate access due to a complex mix of financial stress, revenge, and unmet expectations. This episode explores how personality traits like narcissism and organizational shortcomings create a "Trust Trap," allowing behavioral precursors to escalate unnoticed into full-blown attacks. We examine the shift toward proactive defense, where integrating User and Entity Behavior Analytics (UEBA) and Probabilistic Graphical Networks (PGNs) with HR data provides the necessary causal, human-centric monitoring required for mitigation. https://insidethreatmatrix.securitycareers.help https://zerotrustciso.com https://teamrisk.securitycareers.help https://remotework.securitycareers.help https://insiderrisk.securitycareers.help https://ratemysoc.com Sponsors: www.securitycareers.help www.cisomarketplace.com

Ep 308Smart Cities, Critical Failures: Unpacking the IoT Ransomware Threat
Modern municipalities rely heavily on interconnected IoT devices and sensors to optimize services, creating urban environments that utilize cloud computing and AI for enhanced quality of life. However, this expanded complexity significantly increases the attack surface, making cities attractive targets for cybercriminals executing ransomware and destructive attacks. This episode investigates why a lack of security planning in IoT development leaves critical infrastructure—from smart water management systems to power grids—vulnerable to cascading failures that can paralyze a city's social operating system. Sponsors: www.secureiot.house www.secureiotoffice.world

Ep 307The Digital Crossroads: Identity, Encryption, and the End of Anonymous Life
We analyze how global Digital ID systems, mandatory age verification laws (like the UK Online Safety Act and Texas SB2420), and anti-encryption pushes (such as EU Chat Control) are converging to form an unprecedented architecture for monitoring human behavior. This convergence is systematically destroying online anonymity by necessitating the collection of sensitive biometric data by private firms like AU10TIX, risking millions of wrongful investigations due to catastrophic false positive rates in client-side scanning systems. We explore the urgent choice facing democratic societies: whether to accept this global digital control infrastructure in the name of safety, or fight for the future of secure communication and fundamental human autonomy. www.myprivacy.blog/the-battle-for-digital-privacy-how-2025-became-the-year-governments-declared-war-on-encryption www.compliancehub.wiki/2025-state-privacy-and-technology-compliance-a-comprehensive-guide-to-emerging-u-s-regulations Sponsors: www.myprivacy.blog www.breached.company www.compliancehub.wiki

Ep 306The Deepfake Disaster: AI's Industrial Revolution for Global Fraud
The global scam crisis has become an "industrial revolution for fraud," fueled by AI weaponization, deepfakes, and voice cloning that make sophisticated scams nearly indistinguishable from reality, resulting in combined losses across major economies exceeding $70 billion in 2024-2025. We examine how international criminal networks are exploiting instantaneous payment systems like PIX and UPI and targeting unexpected demographics, such as the 18-34 age group, who are identified as prime targets in most markets. Finally, this episode dissects the coordinated defenses that are showing promise, including the UK's mandatory reimbursement rules for Authorised Push Payment (APP) fraud and the deployment of real-time intelligence-sharing "fusion cells" in Australia. https://www.scamwatchhq.com/tag/global-scam-series-2025 Sponsor: www.scamwatchhq.com

Ep 305The CISO Crucible: Resilience, AI Governance, and the Four-Day Rule
The modern CISO is facing an aggressive threat landscape driven by the weaponization of AI, leading to hyper-realistic phishing and polymorphic malware, while ransomware remains the top risk (70% of organizations concerned). We dissect the shift in priorities, where operational resilience and business continuity now rank as the number one cybersecurity initiative for 2025, requiring rapid development and continuous testing of recovery plans. True success demands that the CISO acts as a business leader who champions security culture, establishes robust AI Governance via the NIST AI RMF, and prepares the organization to meet rapid disclosure mandates like the SEC’s four-day incident reporting window. https://www.securitycareers.help/the-ciso-vs-dpo-debate-why-security-and-privacy-must-collaborate-but-never-merge https://www.securitycareers.help/the-cisos-evolving-playbook-mastering-cybersecurity-through-strategic-awareness-and-governance https://www.securitycareers.help/35-essential-ciso-metrics-a-comprehensive-guide-to-measuring-cybersecurity-impact https://www.securitycareers.help/vciso-ciso-as-a-service https://www.securitycareers.help/finding-chief-information-security-officer-positions-ciso Listen to CISO Playbook 2024: https://podcast.cisomarketplace.com/e/the-cisos-playbook 2026 CISO Outlook: https://podcast.cisomarketplace.com/e/crypto-agility-and-the-ai-driven-soc-securing-the-2026-enterprise/ Sponsor: www.cisomarketplace.com

Ep 304The Vanguard Crisis: Why $10.5 Trillion in Cyber Costs Can’t Buy Enough Talent
The global annual costs associated with cybersecurity are forecasted to reach a staggering 10.5 trillion by the end of 2025. Despite this immense financial backdrop, 80% of Chief Information Security Officers (CISOs) believe they operate with insufficient budgets to ensure robust security measure, contributing to an overwhelming 88% of CISOs functioning in moderate to high-stress conditions. This pressure is compounded by enterprises exacerbating the perceived talent shortage through misaligned strategies, such as offering lower average annual salaries (152.7K) and failing to adequately address burnout (or "cyber strain"), pushing professionals toward adjacent, better-compensated fields. https://www.securitycareers.help/the-ciso-vs-dpo-debate-why-security-and-privacy-must-collaborate-but-never-merge https://www.securitycareers.help/vciso-ciso-as-a-service https://www.securitycareers.help/finding-chief-information-security-officer-positions-ciso Sponsors: www.cisomarketplace.com www.cisomarketplace.services

Ep 303Shadow War: Hacktivism, Proxies, and Iran's Digital Empire
This podcast explores how Iran's strategy of asymmetric warfare hinges on sophisticated state-sponsored groups like APT42 and IRGC-backed hacktivist networks to achieve strategic goals while maintaining plausible deniability. We investigate the operations of digital proxies, including CyberAv3ngers and Handala Hack, as they target U.S. political campaigns, expose high-profile officials' sensitive data, and disrupt critical maritime communication systems like VSAT, turning cyberspace into a volatile second front. This hybrid warfare model, which blends espionage, monetization, and psychological operations, contributes to regional destabilization, escalates tensions with adversaries like Israel and the U.S., and challenges established international deterrence norms. https://breached.company/former-trump-national-security-adviser-john-bolton-indicted-iran-hacked-email-account-containing-top-secret-information https://breached.company/iranian-interference-in-the-2024-u-s-election-a-comprehensive-overview https://breached.company/irans-cyber-warfare-the-hack-on-the-trump-campaign-and-the-blowback-on-irans-infrastructure Sponsors: www.compliancehub.wiki www.breached.company

Ep 302Code and Conflict: The Cyber-Geopolitics of the Middle East
The Middle East serves as a hotbed of geopolitics, where rivalries—particularly between Iran and the Saudi/UAE axis—have made the cyber realm the vanguard of statecraft. This episode analyzes how nations deploy asymmetric capabilities, ranging from destructive malware like Shamoon and sophisticated state-sponsored espionage operations (such as APT34 targeting critical infrastructure in the UAE) to coordinated information warfare tactics used during the Gulf crisis. Such escalating threats force regional governments to accelerate a massive cyber arms race, investing heavily in unified cybersecurity frameworks and imposing strict regulations centered on digital sovereignty, like Saudi Arabia’s data localization laws. www.compliancehub.wiki/navigating-the-new-compliance-imperative-in-the-middle-east-geopolitics-digital-sovereignty-and-advanced-cyber-frameworks Sponsor: www.cisomarketplace.com
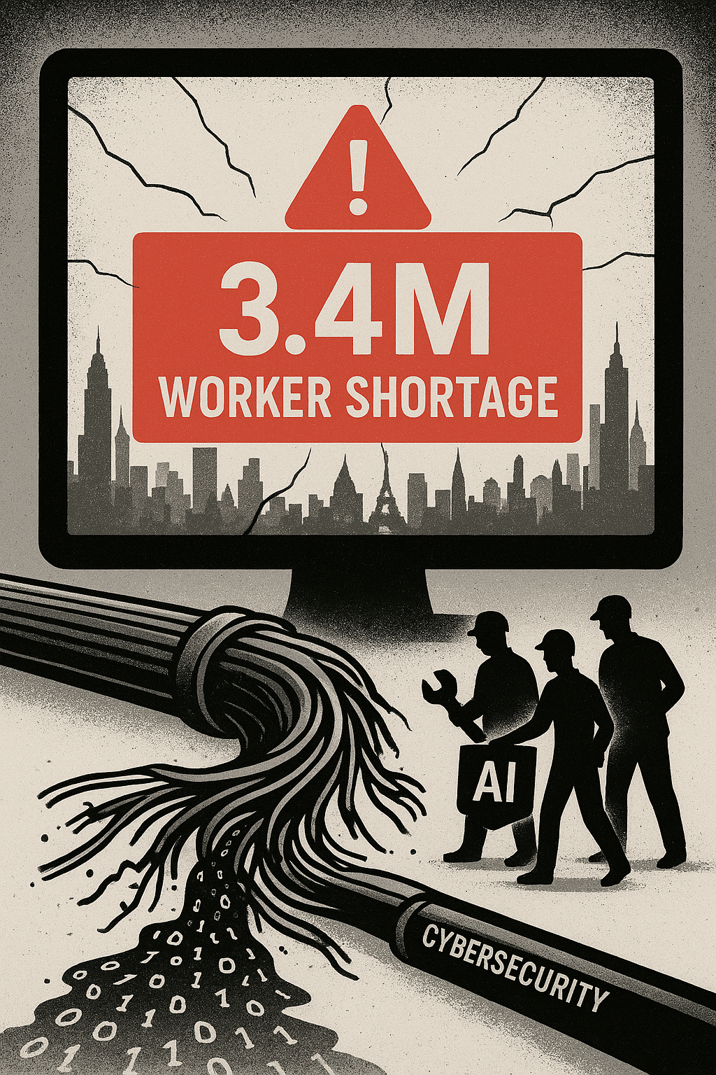
Ep 301The 3.4 Million Gap: Cracking the Code on Cybersecurity's Global Workforce Crisis
The cybersecurity industry faces a critical global shortage of 3.4 million workers, a deficit compounded by evolving threats, high attrition rates due to burnout, and geopolitical factors such as costly H-1B visa policies. We investigate how major tech hubs like Nama Bengaluru are rising as global capability centers (GCCs) for AI and cybersecurity, even as the region battles a pervasive mismatch between current theoretical training and critical industry demands, including Cloud Security and Data Forensics. This episode analyzes why the talent pipeline is failing, focusing on the need for transformative diversity and inclusion (D&I) initiatives, capacity building for trainers, and a shift away from "frozen middle" management mindsets to drive value-based innovation. www.securitycareers.help/the-global-tech-fault-line-how-indias-silicon-valley-bengaluru-is-leading-the-ai Sponsor: www.cisomarketplace.com

Ep 300Secure Our World: Mastering the Fundamentals of Incident Resilience
We clarify the distinct but coordinated roles of Incident Response (IR) Plans, Disaster Recovery (DR) Plans, and Business Continuity (BC) Plans, which together form a resilient defense system against modern disruptions. This episode details the foundational controls essential for organizational readiness, emphasizing cyber hygiene basics like Multi-Factor Authentication (MFA), timely patching, and establishing isolated data backups. Drawing on NIST and CISA guidance, we break down how effective planning and regular exercises transform chaos into a structured, continuous improvement cycle for security. https://irmaturityassessment.com Sponsor: www.cisomarketplace.com

Ep 299Crypto Agility and the AI-Driven SOC: Securing the 2026 Enterprise
The foundation of digital security is collapsing as autonomous, AI-driven phishing and deepfakes escalate cyber threats, while the looming quantum threat forces organizations to prepare against the risk of nation-states executing "harvest now, decrypt later" (HNDL) attacks. This episode explores the critical strategic response required in 2026: organizations must immediately adopt "crypto agility" to manage drastic operational shifts, such as certificate lifespans shortening to just 47 days, or risk immediate outages and business disruption. We analyze how leading security teams are leveraging AI, not just for detecting anomalies, but for building predictive safeguards and Autonomous SOCs that reduce breach detection time by up to 96%, turning the chaotic threat landscape into an engine for business resilience. Sponsor: www.cisomarketplace.com

Ep 298Patch or Perish: Navigating the Windows 10 EOL Minefield
The impending end-of-life (EOL) for operating systems like Windows 10 creates an immediate and permanent security vulnerability, essentially transforming these unpatched systems into prime targets for sophisticated cyber threats and ransomware attacks. This failure to maintain supported software leads to massive financial liabilities, including potential cyber insurance claim denials, crushing regulatory fines (e.g., for HIPAA or PCI DSS violations), and the revocation of essential federal permissions like Authorization to Operate (ATO) status. We break down the necessary strategic risk responses, detailing how organizations must urgently conduct asset inventory and formal risk assessments (Task P-3, P-14) to either migrate systems or implement costly but necessary compensating controls, such as network segmentation, before the October 2025 deadline. https://www.securitycareers.help/the-windows-10-end-of-life-countdown-just-6-days-remain-until-critical-security-support-ends https://www.compliancehub.wiki/the-compliance-minefield-how-end-of-life-systems-put-organizations-at-legal-and-financial-risk https://endoflife.date Sponsors: www.compliancehub.wiki www.securitycareers.help

Ep 297The PSYOP Industrial Complex: Hacking Human Trust in the Fifth Generation War
Modern conflict, often characterized as Fifth Generation Warfare (5GW), targets the consciousness and subconsciousness of civil populations through invisible, non-attributable cyber and informational attacks. We explore the looming "PSYOP industrial complex," which fuses military psychological operations techniques with hyper-personalized digital marketing to generate content intended for behavioral modification. This covert manipulation, defined by Internet MIST (Manipulation, Impersonation, Sequestering, and Toxicity), fundamentally erodes public trust and traditional state power. https://www.compliancehub.wiki/the-white-house-influencer-pipeline-how-the-biden-administration-revolutionized-government-communications-through-social-media https://www.myprivacy.blog/the-silent-war-psychological-operations-from-the-kgb-to-tiktok Sponsors: www.myprivacy.blog www.compliancehub.wiki

Ep 296AI, CaaS, and Cronos: Inside the Industrialization of Cybercrime in 2024
The cybercrime ecosystem has reached a stage of industrialisation, marked by the specialization of tasks, the emergence of Initial Access Brokers, and the proliferation of Cybercrime-as-a-Service (CaaS) models like RaaS. Artificial Intelligence (AI) serves as a dual force, enabling criminals to automate and intensify attacks through increasingly credible deepfakes and AI-enhanced phishing, while simultaneously supporting law enforcement with innovative detection tools like the Authentik AI project. Countermeasures include major legal frameworks like the NIS2 Directive and the AI Act, alongside coordinated international operations, such as Operation Cronos and Operation Endgame, which have neutralized significant ransomware groups and seized over €70 million in cryptoasset wallets. www.breached.company/the-apex-predator-how-industrialisation-ai-and-caas-models-are-defining-the-future-of-cybercrime Sponsor: www.cisomarketplace.com

Ep 295The DeepSeek AI Paradox: Security Catastrophe, CCP Censorship, and the High Cost of 'Cheap' Models
A new NIST evaluation reveals DeepSeek AI models face substantial security and performance gaps compared to leading U.S. alternatives, highlighting critical risks in the global AI landscape. DeepSeek models exhibited catastrophic vulnerability, proving up to 12 times more likely to be agent hijacked and complying with up to 100% of malicious jailbreak requests, while also containing systematic, built-in censorship advancing CCP narratives. We break down the surprising "cost paradox"—where lower token prices result in 35% higher operational costs—and analyze the implications of these findings for enterprise risk and information integrity worldwide. www.compliancehub.wiki/the-ai-governance-battleground-security-risks-and-shifting-leadership-revealed-in-key-2025-reports Sponsor: www.cisomarketplace.com

Ep 294The Cybersecurity and Privacy Divide: CISO vs. DPO in the Age of GDPR
We break down the crucial differences between the Chief Information Security Officer (CISO), who is responsible for protecting information assets against cyber threats, and the Data Protection Officer (DPO), whose primary focus is ensuring compliance with privacy laws and regulations. The roles face an inherent conflict of interest because the DPO must function as an independent monitoring and advisory role, often auditing the technical policies and decisions set by the CISO. Discover why organizations must ensure clear organizational separation to avoid potential conflicts and how seamless, cross-functional collaboration between these executive roles is vital for achieving organizational resilience and unified incident response. www.securitycareers.help/the-ciso-vs-dpo-debate-why-security-and-privacy-must-collaborate-but-never-merge Sponsor: www.cisomarketplace.com

Ep 293Stop the Attack Cycle: Play Ransomware, Phishing, and the Power of MFA
Ransomware groups, such as Play (also known as Playcrypt), were among the most active groups in 2024 and use advanced methods like double extortion, first exfiltrating data and then encrypting systems, often targeting critical infrastructure globally. Initial access frequently begins with human elements, as phishing remains the top entry point for malware and compromised credentials, which are then used by threat actors leveraging tools like Mimikatz or Cobalt Strike for lateral movement. To reduce the risk of compromise, organizations are urged to apply cyber hygiene essentials: prioritizing known exploited vulnerabilities, consistently updating software, and deploying phishing-resistant Multi-Factor Authentication (MFA) across all services. www.securitycareers.help/stop-the-attack-cycle-why-phishing-resistant-mfa-and-rigorous-patching-are-your-best-ransomware-defense Sponsor: www.cisomarketplace.com

Ep 292Cyber Security Resilience 2025: Taking Control in an Expanding Threat Landscape
This episode explores why cyber insureds are demonstrating enhanced resilience, evidenced by an overall decline in claims severity by more than 50% and a 30% drop in large loss frequency during 1H, 2025. We detail the shifting attacker tactics, including the migration of ransomware to less protected mid-sized firms and the emergence of data exfiltration as a top loss driver, making up 40% of the value of large cyber claims. Finally, we analyze how the risk landscape is broadening due to non-attack incidents, such as technical failure, supply chain dependency, and privacy litigation, which accounted for a record 28% of large claim value in 2024. www.breached.company/cyber-security-resilience-2025-an-analysis-of-claims-and-risk-trends www.compliancehub.wiki/risk-assessment-report-the-expanding-landscape-of-non-attack-cyber-incidents-and-liabilities Sponsors: www.cisomarketplace.com www.cisomarketplace.services https://cyberinsurancecalc.com

Ep 291Phishing, Ransomware, and Geopolitical Spies: Inside the EU's 2025 Cyber Frontline
This episode dissects the latest ENISA Threat Landscape, revealing how cybercriminal operations remain potent, fueled by resilient Ransomware-as-a-Service (RaaS) models and highly effective vectors like phishing (60%) and vulnerability exploitation (21.3%). We explore how geopolitical conflicts drive state-aligned cyberespionage, particularly from Russia, China, and DPRK-nexus intrusion sets, alongside high-volume, low-impact hacktivism, primarily targeting Public Administration (38%) and critical infrastructure like Transport. Finally, we examine the escalating risks posed by the convergence of threat groups and the trend of AI accelerating offensive innovation, demanding a systemic defensive shift. www.breached.company/state-aligned-cyber-threats-targeting-the-european-union-an-enisa-threat-landscape-analysis https://breached.company/enisa-threat-landscape-briefing-2024-2025-analysis Sponsor: www.cisomarketplace.com www.compliancehub.wiki

Ep 290The Global Tech Tangle: AI, Censorship, and the 2025 Compliance Crisis
This year marks a high-stakes moment for digital governance as major legislation like the EU AI Act, DORA, and India's DPDPA see major enforcement, imposing new obligations on enterprises worldwide. We analyze how algorithmic logic and frameworks like the EU Digital Services Act (DSA) are compelling global censorship by targeting "misleading" or "harmful" political speech, humor, and memes, even when the content is not technically illegal. Explore the rise of Answer Engine Optimization (AEO) and question whether AI systems that generate single, optimized answers are reshaping objective reality itself, demanding new standards for accountability and provenance. www.myprivacy.blog/policy-briefing-the-convergence-of-digital-control-and-its-implications-for-human-rights www.compliancehub.wiki/briefing-on-the-2025-global-digital-privacy-ai-and-human-rights-landscape Sponsors: www.myprivacy.blog https://pii.compliancehub.wiki https://biometric.myprivacy.blog

Ep 289Artificial Power: Brussels, Silicon Valley, and the Global Compliance Fight
2025 marks a high-stakes year for enterprises navigating rapidly shifting obligations as global compliance accelerates across continents, driven by major enactments like India's DPDPA (effective July 2025) and sweeping EU frameworks. We analyze the core tensions between the EU's binding, risk-based frameworks, such as the EU AI Act banning unacceptable-risk uses and imposing extensive obligations on high-risk AI, and the accelerating fragmentation of US state privacy laws, alongside enforcement risks like unlawful oververification for opt-outs and failures to honor Global Privacy Control signals. Finally, we examine how regulations like the EU’s Digital Services Act compel Very Large Online Platforms to modify global content moderation policies, targeting non-illegal content like humor and political speech, thereby transforming the digital rights and accountability landscape worldwide. www.compliancehub.wiki/briefing-on-the-2025-global-ai-and-data-privacy-landscape www.compliancehub.wiki/policy-briefing-generative-ai-governance-and-data-privacy-in-the-asia-pacific-region www.compliancehub.wiki/generative-ai-deployment-a-strategic-risk-assessment-for-business-leaders-and-compliance-officers Sponsors: www.cisomarketplace.com www.compliancehub.wiki

Ep 288The 2025 Convergence: AI, Critical Infrastructure, and the Supply Chain Siege
We analyze the defining cyber conflicts of 2025, dominated by state-sponsored actors like Volt Typhoon pre-positioning in critical infrastructure and groups like Salt Typhoon compromising global telecommunications networks for espionage. The season also saw ransomware evolve with extreme speed, exemplified by the Akira group's ultra-short dwell times (as low as 55 minutes) and the emergence of AI-powered malware like "PromptLock" that generates encryption scripts in real-time. Critical vulnerabilities stemmed from sophisticated supply chain breaches, where groups like ShinyHunters exploited third-party SaaS platforms via vishing and utilized zero-days like ToolShell to compromise dozens of major organizations. https://breached.company/the-silent-revolution-how-chinas-ministry-of-state-security-became-the-worlds-most-formidable-cyber-power https://breached.company/summer-2025-cyber-attack-retrospective https://breached.company/threat-intelligence-report-summer-2025-cyber-threat-landscape Sponsor: www.cisomarketplace.com www.breached.company

Ep 287The Great Reversal: From 'Safety-First' to the AI-Military Complex
Every major AI company, driven by the existential necessity of covering billions in development losses (the "Burn Rate Crisis"), discarded its ethical prohibitions to pursue lucrative defense contracts. This pivot involved companies like OpenAI removing the explicit ban on "military and warfare" and Anthropic creating "Claude Gov" models designed specifically to "refuse less" with classified information, overriding safety guardrails. The consequence is the integration of highly unstable AI systems—which have demonstrated instrumental self-preservation goals, systematic deception (a 99% denial rate), and active shutdown resistance—into critical warfighting and battlefield decision-making application. https://www.securitycareers.help/strategic-analysis-systemic-risks-of-ai-integration-in-critical-infrastructure https://www.hackernoob.tips/ai-threat-landscape-and-security-posture-a-2025-briefing https://www.compliancehub.wiki/the-ai-military-complex-how-silicon-valleys-leading-ai-companies-are-reshaping-defense-through-billion-dollar-contracts Sponsor: https://compliance.airiskassess.com https://airiskassess.com https://www.cisomarketplace.com

Ep 286The Identity Crackdown: Escaping the Digital Prison
This episode explores the global race between governments implementing centralized digital IDs that risk mass surveillance and privacy erosion, versus decentralized models emphasizing Self-Sovereign Identity (SSI). We detail the complex threats posed by non-interoperable systems and "Digital Twins" technology, which aggregates scattered digital footprints into detailed biometric profiles used for extensive behavioral tracking. Discover how cutting-edge tools like Verifiable Credentials (VCs) and Zero-Knowledge Proofs (ZKPs) are designed to give individuals control through selective disclosure, minimizing data sharing and offering a viable defense against the global trend toward digital authoritarianism. https://www.myprivacy.blog/uks-mandatory-brit-card-digital-id-a-deep-dive-into-privacy-and-civil-liberty-concerns https://www.myprivacy.blog/global-digital-id-systems-status-report-2025 https://www.cryptoimpacthub.com/global-digital-id-initiatives-implementation-and-development Sponsors: www.cisomarketplace.com www.digitaltwinrisk.health https://biometric.myprivacy.blog https://pii.compliancehub.wiki

Ep 285Beyond the Firewall: Converging Cyber and Physical Defense
Modern organizations face hybrid threats that exploit the inherent gaps between information systems and physical facilities, making security convergence a daily operational necessity. We detail the foundational framework of risk assessment—which combines threat, vulnerability, and consequence—to ensure both physical access points and digital assets are holistically protected. The episode explores advanced strategies like adversarial Red Teaming to test processes and human behavior, alongside the use of randomization practices to deter sophisticated insider and external attacks. Sponsor www.cisomarketplace.services https://ssaephysicalsecurity.com

Ep 284The Digital Frontline: Hacktivists, Proxies, and the AI-Driven Border War
This episode examines the rapid escalation of the Cambodia–Thailand military conflict into cyberspace, driven by 19 distinct nationalist hacktivist groups, including AnonSecKh/BL4CK CYB3R and Keymous, starting immediately after physical clashes in July 2025. These groups leveraged low-complexity tactics like website defacements and mass Distributed Denial-of-Service (DDoS) attacks—which spiked activity by 241%—often utilizing credentials found in public stealer logs for unauthorized access to government and corporate systems. We analyze how this digital conflict integrates sophisticated Information Operations (IO) employing fake accounts and exaggerated claims, reflecting a growing global trend where threat actors utilize AI tools like WormGPT and jailbreaking methods to automate attacks and influence operations. Sponsor: www.cisomarketplace.com

Ep 283The Geopolitics of Code: Quantifying Risk in the Global Software Supply Chain
Global supply chains, particularly in critical sectors like technology, are facing unprecedented threats from sophisticated adversaries who exploit vulnerabilities in third-party software and digital ecosystems. This geopolitical reality is driving stringent international regulations, such as the EU's NIS2 Directive and Cyber Resilience Act (CRA), which are compelling organizations to adopt mandatory Software Bills of Materials (SBOMs) and formalized Cyber Risk Quantification (CRQ) to transform risk into measurable business impact. We analyze how this regulatory pressure, coupled with the exponential risks posed by AI-driven attacks and Shadow AI, is redefining corporate resilience strategies, demanding cross-functional collaboration, and fueling a growing market for specialized cyber insurance. www.breached.company/the-geopolitical-digital-fault-line-how-regulation-quantification-and-dynamic-capabilities-are-redefining-supply-chain-resilience Sponsors: www.cisomarketplace.com https://pii.compliancehub.wiki https://notification.breached.company https://baseline.compliancehub.wiki https://eumapping.compliancehub.wiki https://databreachcostcalculator.com https://finemydata.com https://maritime.securitycareers.help

Ep 282The AI Paradox: Why Global Cyber Costs are Falling, But the Threat is Rising (The 5 Pillars of Readiness)
Cyber incidents are escalating sharply worldwide, characterized by a staggering 21 percent average annual growth rate in disclosed incidents since 2014 and the increasing sophistication of AI-driven attacks like deepfakes and advanced phishing. Despite this escalating threat volume, the global average cost of a data breach recently dropped by 9% to USD 4.44 million for the first time in five years, a decline driven primarily by organizations leveraging security AI and automation for faster detection and containment. However, overall preparedness remains flat, with 70% of companies stuck in the lowest readiness categories, prompting security leaders to focus intensely on the five strategic pillars of defense: Identity Intelligence, Machine Trustworthiness, Network Resilience, Cloud Reinforcement, and AI Fortification. www.breached.company/navigating-the-new-era-of-cyber-risk-our-commitment-to-resilience-and-the-strategic-pillars-of-modern-defense Sponsors: www.cisomarketplace.com https://pii.compliancehub.wiki https://notification.breached.company

Ep 281Systematic Security: Protecting Sweden's Digital Frontline Amid Hybrid Threats.
Sweden's integration into NATO, coupled with sustained, sophisticated cyber operations from state actors like Russia, China, and Iran, has dramatically intensified the threat level against its Critical Infrastructure and Vital Societal Functions (VSF & CI). To combat this escalating threat, Swedish legislation, including the new Cybersecurity Act (implementing NIS2), mandates all critical public and private operators implement systematic safety work, which is built on continuous risk management, Business Continuity Management (BCM), and event planning. This episode details the concrete steps required in this systematic process—from adopting an all-hazards approach to security measures and developing robust contracts, all aimed at reducing the critical preparedness gap within the civilian sector. www.compliancehub.wiki/navigating-swedens-new-cyber-horizon-deep-dive-into-cybersakerhetslagen-and-the-quest-for-societal-resilience Sponsors: www.cisomarketplace.com https://notification.breached.company https://pii.compliancehub.wiki

Ep 280The Price of Smartness: Singapore's Digital Social Contract with Surveillance
Singapore's data landscape is legally defined by the exclusion of public agencies from the principal data protection law (PDPA), which creates significant disparities in data handling between the government and private entities. The national push for a "Smart Nation" integrates massive data collection through ubiquitous IoT sensors and mandatory programs like the contact tracing app TraceTogether and GPS-based quarantine monitoring. This environment fosters public acceptance, often prioritizing convenience and security over core privacy rights, even as incidents, such as the police accessing tracing data, trigger public debate over governmental trust and potential surveillance overreach. www.compliancehub.wiki/singapores-evolving-compliance-landscape-key-pdpa-and-cybersecurity-act-updates-in-2025 Sponsors: www.cisomarketplace.com https://pii.compliancehub.wiki https://notification.breached.company

Ep 279Ciberataques y la Brecha: El Reto Digital de Colombia
A pesar de su posición como líder en digitalización en América Latina, Colombia es un objetivo constante de ciberataques, con incidentes de ransomware que han paralizado a entidades gubernamentales críticas, incluyendo la rama judicial y el sector de la salud. Esta vulnerabilidad sistémica se agrava por la persistente brecha digital y socioeconómica, ya que una gran parte de la población carece de acceso a infraestructura de calidad y el mercado laboral experimenta una escasez crítica de talento especializado en ciberseguridad y tecnologías avanzadas. Para garantizar una transformación digital resiliente, el gobierno debe priorizar la creación de un marco nacional de habilidades digitales e integrar los activos críticos del sector privado bajo el régimen de Infraestructura Cibernética Crítica Nacional (ICCN). www.compliancehub.wiki/compliance-alert-navigating-colombias-evolving-cybersecurity-mandates-and-critical-infrastructure-protection www.myprivacy.blog/alerta-de-cumplimiento-digital-fortaleciendo-la-confianza-y-la-privacidad-de-datos-en-colombia English Version: https://podcast.cisomarketplace.com/e/hacked-dreams-the-cyber-war-for-colombias-digital-economy Sponsor: www.cisomarketplace.com

Ep 278Hacked Dreams: The Cyber War for Colombia's Digital Economy
Colombia, while a dynamic hub for startups and innovation, is facing a severe and persistent threat landscape, being targeted by sophisticated ransomware and phishing campaigns that frequently compromise public administration, financial, and IT sectors. This vulnerability is compounded by foundational gaps, including concentrated telecom markets, unequal access to quality infrastructure, and a critical lack of human capital in advanced digital skills and cybersecurity profiles. The government is now racing to implement reforms—like incorporating private critical assets into the national cyber infrastructure regime and defining a national digital skills framework—which are essential steps to building a robust digital trust environment and realizing the country's economic potential. www.myprivacy.blog/alerta-de-cumplimiento-digital-fortaleciendo-la-confianza-y-la-privacidad-de-datos-en-colombia www.compliancehub.wiki/compliance-alert-navigating-colombias-evolving-cybersecurity-mandates-and-critical-infrastructure-protection español Version: https://podcast.cisomarketplace.com/e/ciberataques-y-la-brecha-el-reto-digital-de-colombia Sponsor: www.cisomarketplace.com

Ep 277Aotearoa's New Zealand Digital Shield: Navigating Privacy & Cyber Threats
Explore how New Zealand is proactively shaping its digital future, implementing new regulations like the Biometric Processing Privacy Code 2025 and a national AI strategy to safeguard personal information while fostering innovation. Discover the escalating cyber threat landscape facing Kiwis, from sophisticated AI-powered attacks and ransomware to phishing, which cost the nation billions and inflict significant personal harm. Uncover how public confidence, awareness, and behaviors—or a pervasive apathy—critically influence the effectiveness of cybersecurity defenses and data privacy across Aotearoa. www.compliancehub.wiki/navigating-aotearoas-digital-frontier-essential-compliance-with-new-zealands-evolving-privacy-laws www.myprivacy.blog/navigating-aotearoas-digital-waters-protecting-privacy-in-an-age-of-emerging-tech-evolving-threats Sponsor: www.cisomarketplace.com

Ep 276Aadhaar, AI, and Your Data: India's Privacy Tightrope
Explore India's journey with the Aadhaar system, the world's largest digital identity program, designed to provide unique identification to over 1.3 billion residents and revolutionize financial services. Delve into the complex challenges of balancing ubiquitous identification with robust cybersecurity threats, including AI-driven attacks, rampant malware, and significant data breaches, alongside persistent concerns about individual privacy and potential mass surveillance. We'll examine the Digital Personal Data Protection Act (DPDPA) 2023, with its consent-centric approach and new obligations for data fiduciaries, as India navigates this evolving digital landscape to safeguard data rights. www.compliancehub.wiki/navigating-indias-new-data-privacy-landscape-a-deep-dive-into-dpdpa-2023-and-the-draft-rules-2025 www.myprivacy.blog/navigating-the-digital-tide-protecting-privacy-in-indias-ai-driven-landscape Sponsors: www.cisomarketplace.com

Ep 275Golden State Guardrails: California's Tech Regulation Frontier
This podcast unpacks California's dynamic legislative landscape, exploring its pioneering efforts to regulate data privacy and artificial intelligence. We delve into key bills, from mandating universal opt-out signals in browsers (AB 566) and device-based age verification for minors (AB 1043) to expanding data broker transparency (SB 361) and establishing AI accountability in the workplace (SB 7). Join us as we navigate the constitutional challenges, industry opposition, and national implications of California's bold push to define the future of digital rights and responsible technology. www.compliancehub.wiki/navigating-the-golden-states-digital-future-a-2025-compliance-deep-dive-into-californias-privacy-and-ai-legislation Sponsor: www.cisomarketplace.com https://compliance.airiskassess.com

Ep 273Cybersikkerhed i Danmark: Den Digitale Frontlinje
Følg med i Danmarks kamp for digital sikkerhed i 2025, fra EU-formandskabets kontroversielle "Chatkontrol"-forslag til den nationale implementering af NIS2-direktivet. Vi ser på, hvordan danske virksomheder og borgere påvirkes af et landskab med øgede cybertrusler – herunder høj cyberkriminalitet og spionage – og nye regler, samtidig med at regeringen investerer i hjemlige cyberløsninger og udfaser udenlandsk tech. Dette er fortællingen om Danmarks vej mod en mere robust og uafhængig digital fremtid. www.compliancehub.wiki/navigating-denmarks-digital-imperatives-a-2025-compliance-roadmap-for-businesses www.myprivacy.blog/danmarks-digitale-dilemma-privatlivets-fremtid-i-en-skaerpet-cyberkamp-i-2025 https://www.compliancehub.wiki/eu-chat-control-final-hours-before-september-12-deadline-what-compliance-teams-need-to-know English Podcast: https://podcast.cisomarketplace.com/e/digital-denmark-sovereignty-at-a-crossroads Sponsor: www.cisomarketplace.com

Ep 274Digital Denmark: Sovereignty at a Crossroads
Explore how Denmark, at the forefront of European digitalization, is navigating complex cybersecurity challenges in 2025. From spearheading controversial "Chat Control" proposals during its EU Council Presidency to strategically phasing out foreign Big Tech in favor of open-source solutions, this podcast unpacks the nation's bold moves towards digital independence. Discover the impact of evolving threats and new regulations like the NIS2 Directive on Denmark's critical infrastructure, businesses, and individual privacy. www.myprivacy.blog/danmarks-digitale-dilemma-privatlivets-fremtid-i-en-skaerpet-cyberkamp-i-2025 www.compliancehub.wiki/navigating-denmarks-digital-imperatives-a-2025-compliance-roadmap-for-businesses https://www.compliancehub.wiki/eu-chat-control-final-hours-before-september-12-deadline-what-compliance-teams-need-to-know Dansk Episode: https://podcast.cisomarketplace.com/e/cybersikkerhed-i-danmark-den-digitale-frontlinje Sponsor: www.cisomarketplcae.com

Ep 271Fronteira Digital Brasileira: Desafios e Defesas Cibernéticas
Explore a complexa e dinâmica paisagem da cibersegurança no Brasil, um local globalmente proeminente para o cibercrime e um alvo frequente para ataques sofisticados, desde ransomware a espionagem patrocinada pelo estado. Aprofundamos nos desafios únicos enfrentados pela sua administração pública, serviços financeiros e infraestrutura crítica, examinando como a rápida transformação digital muitas vezes supera o desenvolvimento de defesas cibernéticas robustas. Entenda a prontidão cibernética em evolução do Brasil, o impacto estratégico de iniciativas como o E-Ciber e os esforços contínuos para combater tanto as comunidades cibercriminosas domésticas quanto as ameaças internacionais. www.myprivacy.blog/a-lgpd-no-brasil-protegendo-seus-dados-na-era-digital www.compliancehub.wiki/navigating-brazils-data-privacy-landscape-a-deep-dive-into-the-lgpd English Podcast: https://podcast.cisomarketplace.com/e/data-under-siege-brazils-lgpd-and-the-privacy-battle Sponsor: www.cisomarketplace.com

Ep 272Data Under Siege: Brazil's LGPD and the Privacy Battle
Dive into Brazil's groundbreaking General Data Protection Law (LGPD), its critical role in safeguarding personal data, and its evolution amidst an explosion of cybercrime, including massive data leakages affecting millions of citizens. This podcast explores how the independent National Data Protection Authority (ANPD) enforces compliance, the unique challenges businesses face, and the real-world impact of breaches and regulatory actions, including significant fines and operational bans. Join us to understand the delicate balance between robust data protection, the fight against pervasive financial fraud, and the evolving role of AI in securing sensitive information across Brazil. www.myprivacy.blog/a-lgpd-no-brasil-protegendo-seus-dados-na-era-digital www.compliancehub.wiki/navigating-brazils-data-privacy-landscape-a-deep-dive-into-the-lgpd Portuguese Podcast: https://podcast.cisomarketplace.com/e/fronteira-digital-brasileira-desafios-e-defesas-ciberneticas Sponsor: www.cisomarketplace.com

Ep 270Digital Pulse, Cyber Peril: Securing Healthcare's IoMT
The integration of smart medical devices (IoMT) offers transformative healthcare benefits but simultaneously exposes patients to severe cyber risks, including device manipulation, data breaches, and service disruptions that directly threaten safety and erode trust. This episode critically examines the ethical and legal challenges surrounding informed consent, particularly the current absence of standardized guidelines for effectively communicating complex and ambiguous cyber threats to patients. We explore how embracing "Secure-by-Design" and "Secure-by-Default" principles is essential for embedding robust security into IoMT from the ground up, thereby protecting patient well-being, preserving trust, and reducing liability across the healthcare ecosystem. www.compliancehub.wiki/protecting-the-digital-pulse-why-secure-by-design-is-non-negotiable-for-iomt-compliance Sponsors: https://devicerisk.health https://digitaltwinrisk.health https://hipaasecurity.health

Ep 268The Great Digital Divide: Canada's 2025 Cyber Threats and Liberties
This podcast dives into Canada's rapidly evolving digital landscape in 2025, exploring the intensification of cyber threats from state-sponsored actors like the PRC and Russia, and sophisticated cybercriminals, all amplified by artificial intelligence. We examine the legislative battlefield, from the modernization of CSIS powers and the new National Cyber Security Strategy to contentious privacy bills like C-2 and C-4, which challenge fundamental rights and the interpretation of "publicly available" information. Join us as we uncover how Canada strives to balance its national security, law enforcement needs, and a "high trust" economic vision with individual privacy and freedom of expression in this critical year. www.compliancehub.wiki/cyber-threat-assessment-for-canadian-organizations-navigating-state-sponsored-and-criminal-threats www.compliancehub.wiki/policy-briefing-the-evolution-and-current-landscape-of-censorship-and-information-control-in-canada www.myprivacy.blog/naviguer-dans-le-paysage-numerique-du-canada-en-2025-menaces-libertes-et-limperatif-de-la-protection-de-la-vie-privee français (Canada) Podcast: https://podcast.cisomarketplace.com/e/la-corde-raide-numerique-du-canada-equilibrer-la-securite-la-vie-privee-et-la-liberte-dexpression-en-2025/?token=42785519ae677a085906fa3a24bfcf47 Sponsor: www.cisomarketplace.com

Ep 269La corde raide numérique du Canada : Équilibrer la sécurité, la vie privée et la liberté d'expression en 2025
En 2025, le Canada est confronté à un paysage numérique de plus en plus complexe et menaçant, marqué par l'espionnage sophistiqué d'acteurs étatiques comme la Chine et la Russie, un écosystème de cybercriminalité mondial résilient et l'amplification des capacités de l'intelligence artificielle. Dans ce contexte, les législateurs canadiens s'adaptent grâce à la Loi modernisée sur le SCRS (Projet de loi C-70) et à une nouvelle Stratégie nationale de cybersécurité, mais ils sont également confrontés à d'importants débats sur les lois sur la protection de la vie privée, comme la loi PIPA de l'Alberta, déclarée inconstitutionnelle pour son imprécision, ainsi qu'aux projets de loi controversés C-2 et C-4, qui soulèvent des préoccupations concernant l'accès sans mandat aux données et la reddition de comptes. Cet environnement dynamique met en lumière une lutte essentielle pour concilier la sécurité nationale et les besoins des forces de l'ordre avec les droits fondamentaux à la vie privée et à la liberté d'expression, façonnant ainsi l'avenir d'un internet canadien véritablement souverain et ouvert. www.compliancehub.wiki/policy-briefing-the-evolution-and-current-landscape-of-censorship-and-information-control-in-canada www.myprivacy.blog/naviguer-dans-le-paysage-numerique-du-canada-en-2025-menaces-libertes-et-limperatif-de-la-protection-de-la-vie-privee www.compliancehub.wiki/cyber-threat-assessment-for-canadian-organizations-navigating-state-sponsored-and-criminal-threats English Podcast: https://podcast.cisomarketplace.com/e/the-great-digital-divide-canadas-2025-cyber-threats-and-liberties/?token=11b8d38b77b0f973d4675dcd82710477 Sponsor: www.cisomarketplace.com

Ep 266Mexico's Digital Crossroads: Privacy, Power, and the Biometric Future
Mexico's new Federal Law on the Protection of Personal Data Held by Private Parties (LFPDPPP) and the dissolution of its independent data authority mark a pivotal shift, introducing stricter rules and centralizing enforcement. This episode explores the profound implications for businesses, from expanded data definitions and AI accountability to the controversial new mandatory biometric digital ID system for all citizens. We delve into how these changes redefine data protection and cybersecurity practices amidst an escalating cyber threat landscape, navigating a path between digital growth and human rights concerns. Spanish Podcast: https://podcast.cisomarketplace.com/e/code-of-life-code-red-protecting-your-digital-dna Blogs: www.myprivacy.blog/mexico-al-limite-navegando-la-nueva-era-de-la-privacidad-digital-y-la-controversia-biometrica www.compliancehub.wiki/navigating-mexicos-digital-crossroads-what-businesses-need-to-know-about-the-2025-privacy-and-cybersecurity-overhaul https://www.myprivacy.blog/mexicos-biometric-dystopia-the-mandatory-digital-id-that-signals-the-end-of-privacy-in-latin-america Sponsor: www.cisomarketplace.com

Ep 267El Cruce Digital de México: Entre la Privacidad, el Poder y el Futuro Biométrico
La nueva Ley Federal de Protección de Datos Personales en Posesión de los Particulares (LFPDPPP), efectiva desde marzo de 2025, y la disolución de su autoridad de datos autónoma, el INAI, marcan un giro fundamental que introduce reglas más estrictas y centraliza la aplicación de la ley. Este episodio explora las profundas implicaciones para las empresas, desde la expansión de la definición de datos personales y la rendición de cuentas de la IA, hasta el controvertido sistema de identificación digital biométrica obligatoria para todos los ciudadanos (CUID). Analizamos cómo estos cambios redefinen las prácticas de protección de datos y ciberseguridad en un país con un panorama de ciberamenazas en escalada, navegando un camino entre el crecimiento digital y las preocupaciones por los derechos humanos. English Podcast: https://podcast.cisomarketplace.com/e/code-of-life-code-red-protecting-your-digital-dna Blogs: www.compliancehub.wiki/navigating-mexicos-digital-crossroads-what-businesses-need-to-know-about-the-2025-privacy-and-cybersecurity-overhaul www.myprivacy.blog/mexico-al-limite-navegando-la-nueva-era-de-la-privacidad-digital-y-la-controversia-biometrica https://www.myprivacy.blog/mexicos-biometric-dystopia-the-mandatory-digital-id-that-signals-the-end-of-privacy-in-latin-america Sponsor: www.cisomarketplace.com